遊戲娛樂
遊戲娛樂
·
10分鐘
·
10分鐘
W.Ting
已更新
已更新
已更新
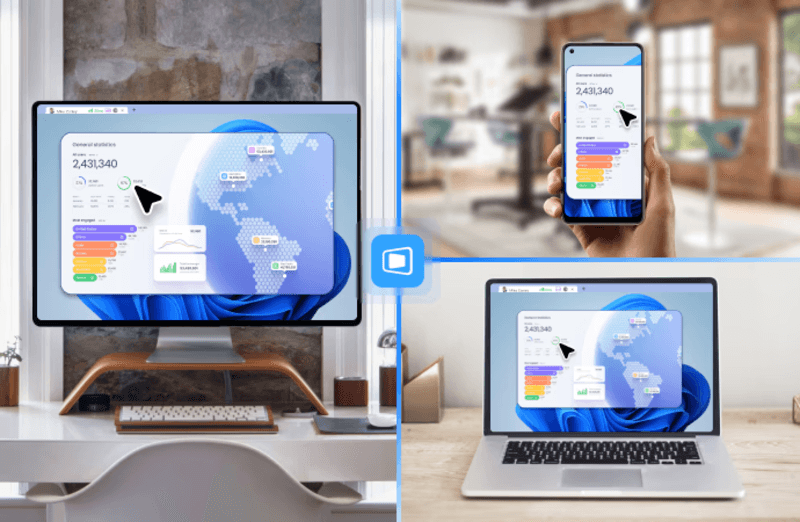
不在家時,或者在外休息的時候,想暢玩留在電腦裡的遊戲庫?無論是通勤或外出,想遠端連線到家中的高效能電腦「續玩」進度,卻發現困難重重?
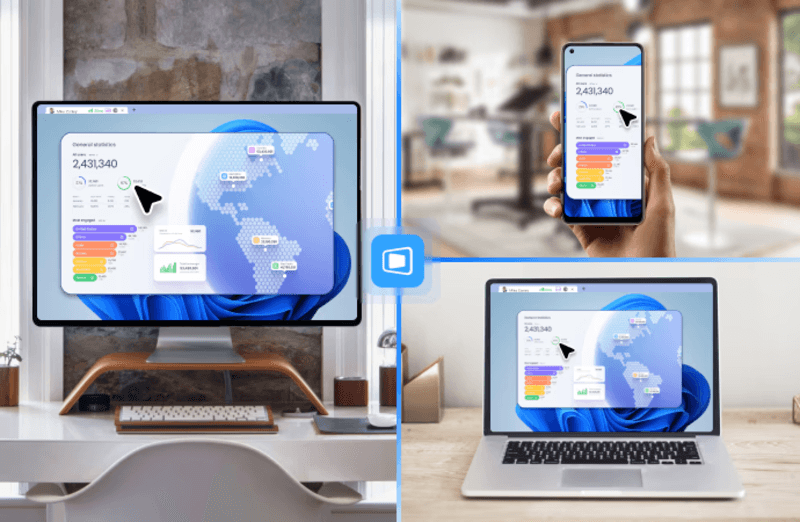
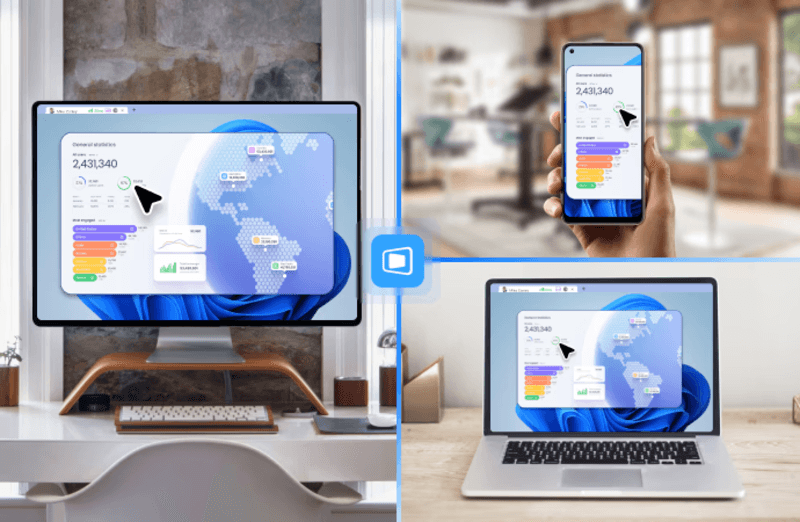
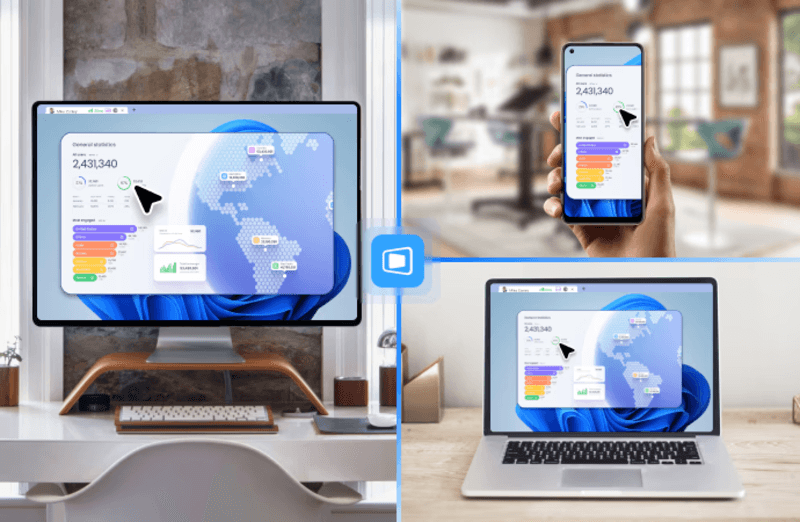
無論是用手機還是平板,你都能隨時遠端操控家裡的電腦,暢玩 Steam、Epic 或 Windows 獨佔遊戲。別再讓距離中斷你的遊戲體驗!本文將為你詳細解析三種實用的遠端遊玩妙招,從高畫質低延遲的 DeskIn到專為遊戲打造的 Parsec以及雲端遊戲服務,一步步教你如何輕鬆設定,實現隨時隨地遠端玩遊戲實現你遊戲的夢想。
更多延伸閲讀
在眾多遠端方案中,DeskIn 憑藉其低延遲、操作流暢穩定脫穎而出。不同於 TeamViewer、AnyDesk 這類以辦公為主的遠端軟體,DeskIn 確保手機上的每一次操作都如本地設備般即時響應。它專為遠端遊戲打造的串流技術,結合 ZeroSync®引擎 支援的 RTC(Real-Time Communication)技術,能將延遲壓低至 ≤40毫秒,提供流暢無比的操作體驗,不論你是你在外用手機遠端連回家中電腦,正準備對魔王發動致命一擊時,還是和朋友連綫遠程打遊戲,都能享受流暢遊戲體驗。
DeskIn 深刻理解遊戲玩家的需求。DeskIn 提供全面的遊戲控制解決方案:手機上可自訂組合按鍵,方便快速施展複雜操作;同時支援外接遊戲手把,並兼容市面上大部分手把設備;更內建遊戲模式,能將電腦鍵鼠操作完美映射到手機,並自動啟動 3D 視角,讓你在手機上也能享受如同本地遊玩的完整操作體驗。這徹底解決了在手機上暢玩PC遊戲的操控難題。除了手機,DeskIn 同樣支援在另一台電腦上遠端操作你的遊戲主機,保持低延遲和高畫質體驗,方便在辦公室或其他電腦環境繼續遊戲進度,並讓在 Mac 上遠端遊玩 Windows 獨佔遊戲變得輕鬆自如,這是普通遠端桌面軟體根本無法提供的專業遊戲體驗。

DeskIn:為遠端遊戲而生的遠端軟體首選
極致畫質還原 - 提供最高4K60FPS / 2K144FPS畫質與 4:4:4無損色度採樣,完美呈現遊戲開發者設定的豐富、飽滿視覺體驗。
流暢遊戲體驗 - 業界領先的 <40ms 超低延遲技術,確保操作與畫面同步,告別卡頓,暢玩快節奏遊戲。
專屬遊戲控制台 - 支援自訂組合按鈕、自由放置與調整大小,打造您專屬的手機虛擬手把,輕鬆施展複雜連招。
全平台無縫連接 - 全面支援 Windows、mac、iOS 與 Android,打破裝置界限,隨時隨地遠端遊玩您的遊戲庫。
3D 視角模式 – 遊戲模式自動啟動 3D 視角,提供身臨其境的遊玩體驗。
外接手把完美適配 – 支援市面上大部分遊戲手把,手機亦可流暢操作,兼顧個人習慣與多樣設備。
手機遊戲鏡像與直播 – 可將手機畫面鏡像回電腦,方便遠端遊玩或進行直播分享,操作靈活便捷。
瞭解了DeskIn的強大優勢後,接下來我們將透過簡單明瞭的圖文步驟,手把手教您如何從頭開始設定,輕鬆實現用手機遠端暢玩電腦遊戲。
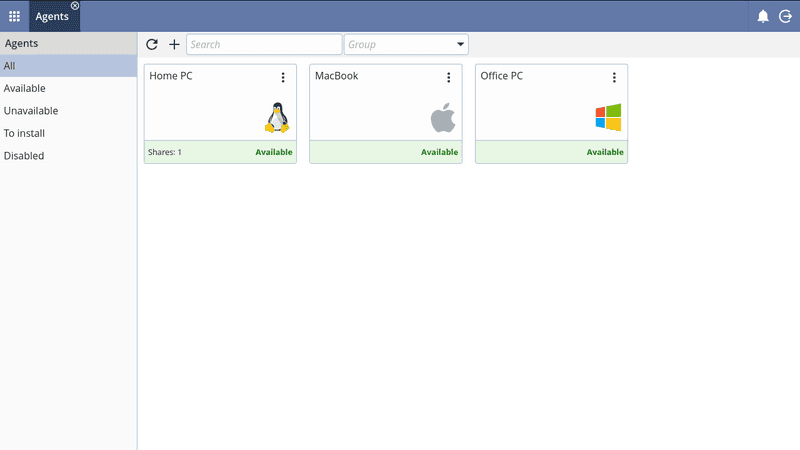
在本地裝置和遠端電腦上提前安裝 DeskIn ,如果是第一次使用,可以註冊一個免費帳號並登入。註冊帳號不僅能讓你的連線更加安全,還方便管理多台裝置,同時可統一管理付費方案,確保使用體驗更順暢。

打開本地設備上的DeskIn,在手機上輸入連線密碼。密碼屬於臨時密碼,也可以自行修改,比如可以自訂臨時密碼,改成簡單好記的密碼如1234567c。如果手機和電腦都登入了同一個帳號,則無需輸入密碼即可快速連線。

點擊「連線」,瞬間即可完成連線,快速進入遊戲體驗。

連線成功後,您可直接透過手機觸控螢幕,流暢操控電腦上的遊戲,隨時隨地暢玩 Steam 或 Epic 遊戲庫中的珍藏大作。無論是《楓之谷》、《天堂》、《GTA5》還是《魔物獵人》,都能在手機上享受完整操作體驗,讓遠端遊玩與本地遊戲一樣流暢。

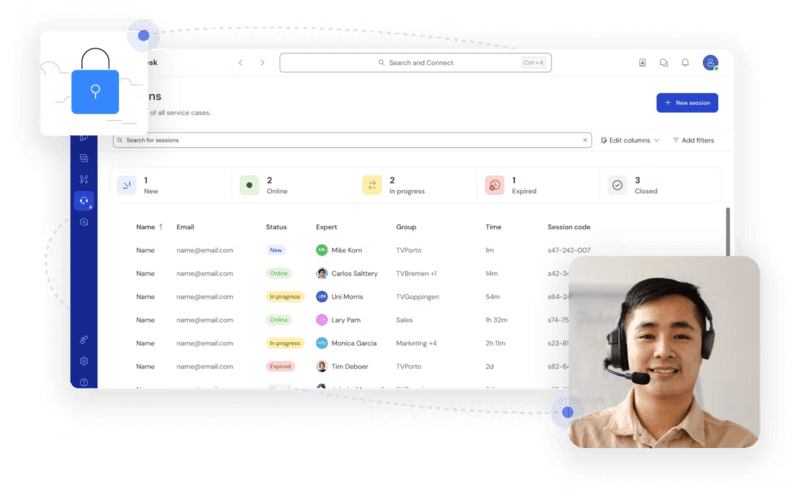
Parsec 是目前市面上另一款優秀的遠端軟體之一。它採用先進的硬體加速編碼技術,能夠提供接近本地遊戲的流暢體驗,延遲低至個位數毫秒。相比其他遠端桌面軟體,Parsec 專為遊戲優化,支援 60FPS 高幀率串流,並且設定簡單易用。無論是 AAA 大作還是獨立遊戲,Parsec 都能讓您在手機上享受完整的 PC 遊戲體驗,真正實現隨時隨地遠端暢玩遊戲的自由。Parsec 行動端目前僅支援 Android安裝,不支援 iOS安裝,透過Android手機或外接適配Android的手把可以低延遲遠端遊玩 PC 遊戲,但不提供手機端自定義PC組合按鍵功能,操控靈活性上比 DeskIn還是差一些。所以接下來的方案主要演示電腦控制電腦遠端玩遊戲。
在兩台電腦上都下載並安裝 Parsec ,創建 Parsec 帳戶並在兩台設備上登入。

打开软件,登录账号。第一台电脑点击图中蓝色的「Share」,它会生成一个连接,将连接复制发给另一台电脑。
接下来是另一台电脑的操作,复制第一台电脑发来的链接,將連結貼在程式右下角方格中並按下「Join」即可。

連接成功後,你會看到桌面,可以直接操作遊戲,就像在本地玩一樣。
如果你沒有頂級電腦或希望減少硬體負擔,雲端遊戲服務是另一個理想選擇。透過 GeForce NOW、Xbox Cloud Gaming 或 Steam Cloud Play 等平台,遊戲運行在雲端伺服器上,手機、平板或輕薄筆電即可串流遊玩高畫質遊戲,完全不需擔心本地硬體性能。
操作簡單:只需安裝官方 App 或透過瀏覽器登入帳號,即可立即開始遊戲。
零距離限制:不論在家、通勤途中或朋友家,都能隨時暢玩 PC 或主機遊戲。
節省成本:不必購買高效能電腦或顯卡,即可體驗最新遊戲大作。
自動更新與存檔:遊戲在雲端運行,自動保持最新版本並同步進度,隨時隨地續玩。
缺點與限制:
遊戲庫受限,部分遊戲無法雲端遊玩。
多數平台需訂閱月費,長期成本不低。
對網路速度要求高,延遲與畫質受限。
無法自由安裝 MOD 或自訂設定。
某些服務在亞洲地區尚未正式開放。
若你希望「自由控制自己的電腦、暢玩所有遊戲、同時兼顧工作與娛樂」,DeskIn 是更靈活且零月費的理想選擇。
選擇你喜歡的雲端遊戲平台,創建帳號並安裝官方 App,或直接用瀏覽器登入。

在平台內選擇你想玩的遊戲,點擊「開始遊玩」即可,畫面會直接串流到你的裝置,手機或筆電也能流暢操作。
大多數雲端平台支援虛擬手把或外接控制器,讓你在手機或平板上也能享受完整遊戲操作體驗。
無論你是想在通勤途中續玩 Steam 遊戲,還是用筆電在咖啡廳體驗最新 AAA 大作,DeskIn都能讓你隨時隨地暢玩,不受距離與硬體限制。
手機遠端玩電腦遊戲需要在電腦安裝遠程軟體作為主機端,手機安裝對應 APP 作為客戶端,通過網路串流實現遊戲畫面和操控傳輸。最重要的是選擇一款合適的遠程軟體推薦,首推 DeskIn,專為遊戲優化,實現高畫質0延遲體驗,手機端操控響應極快,支援自定義觸控按鍵映射,讓手機也能流暢操作電腦遊戲。
iPhone 或 iPad 用戶需要注意平台支援。Parsec 不支援 iOS,無法在手機或平板上遠端遊玩,而 DeskIn 完全支援 iOS,低延遲、高畫質,並提供虛擬手把與按鍵映射功能,是 iOS 用戶的最佳選擇。
選擇遊戲遠程軟體需重點考慮延遲控制、畫質表現、網路適應性和硬體相容性等因素。強烈推薦 DeskIn,這款軟體專為遊戲場景打造,實現高畫質0延遲的卓越體驗,即使在複雜的網路環境下也能保持穩定連接,讓遠程遊戲如同本地操作般流暢。
遠端遊戲技術已經成熟到能提供真正流暢的跨裝置體驗。無論你想在通勤途中用手機繼續Steam進度,還是在朋友家用 Mac 暢玩Windows獨佔大作,本文介紹的 2 大方案都能滿足你的需求。
在眾多選擇中,DeskIn 無疑是最佳推薦。其專為遊戲打造的0延遲技術,配合高畫質4:4:4色彩還原和自定義遊戲按鍵功能,徹底解決了手機遠端玩電腦遊戲的核心痛點。相比其他方案,DeskIn 不僅設定簡單,更在複雜網路環境下保持卓越穩定性,讓每一次操作都如本地般即時響應。
現在就下載 DeskIn,開啟你的隨時隨地遊戲新體驗吧!不再受距離限制,讓高品質的PC遊戲庫真正為你所用,享受前所未有的遊戲自由度。
不在家時,或者在外休息的時候,想暢玩留在電腦裡的遊戲庫?無論是通勤或外出,想遠端連線到家中的高效能電腦「續玩」進度,卻發現困難重重?
無論是用手機還是平板,你都能隨時遠端操控家裡的電腦,暢玩 Steam、Epic 或 Windows 獨佔遊戲。別再讓距離中斷你的遊戲體驗!本文將為你詳細解析三種實用的遠端遊玩妙招,從高畫質低延遲的 DeskIn到專為遊戲打造的 Parsec以及雲端遊戲服務,一步步教你如何輕鬆設定,實現隨時隨地遠端玩遊戲實現你遊戲的夢想。
更多延伸閲讀
在眾多遠端方案中,DeskIn 憑藉其低延遲、操作流暢穩定脫穎而出。不同於 TeamViewer、AnyDesk 這類以辦公為主的遠端軟體,DeskIn 確保手機上的每一次操作都如本地設備般即時響應。它專為遠端遊戲打造的串流技術,結合 ZeroSync®引擎 支援的 RTC(Real-Time Communication)技術,能將延遲壓低至 ≤40毫秒,提供流暢無比的操作體驗,不論你是你在外用手機遠端連回家中電腦,正準備對魔王發動致命一擊時,還是和朋友連綫遠程打遊戲,都能享受流暢遊戲體驗。
DeskIn 深刻理解遊戲玩家的需求。DeskIn 提供全面的遊戲控制解決方案:手機上可自訂組合按鍵,方便快速施展複雜操作;同時支援外接遊戲手把,並兼容市面上大部分手把設備;更內建遊戲模式,能將電腦鍵鼠操作完美映射到手機,並自動啟動 3D 視角,讓你在手機上也能享受如同本地遊玩的完整操作體驗。這徹底解決了在手機上暢玩PC遊戲的操控難題。除了手機,DeskIn 同樣支援在另一台電腦上遠端操作你的遊戲主機,保持低延遲和高畫質體驗,方便在辦公室或其他電腦環境繼續遊戲進度,並讓在 Mac 上遠端遊玩 Windows 獨佔遊戲變得輕鬆自如,這是普通遠端桌面軟體根本無法提供的專業遊戲體驗。

DeskIn:為遠端遊戲而生的遠端軟體首選
極致畫質還原 - 提供最高4K60FPS / 2K144FPS畫質與 4:4:4無損色度採樣,完美呈現遊戲開發者設定的豐富、飽滿視覺體驗。
流暢遊戲體驗 - 業界領先的 <40ms 超低延遲技術,確保操作與畫面同步,告別卡頓,暢玩快節奏遊戲。
專屬遊戲控制台 - 支援自訂組合按鈕、自由放置與調整大小,打造您專屬的手機虛擬手把,輕鬆施展複雜連招。
全平台無縫連接 - 全面支援 Windows、mac、iOS 與 Android,打破裝置界限,隨時隨地遠端遊玩您的遊戲庫。
3D 視角模式 – 遊戲模式自動啟動 3D 視角,提供身臨其境的遊玩體驗。
外接手把完美適配 – 支援市面上大部分遊戲手把,手機亦可流暢操作,兼顧個人習慣與多樣設備。
手機遊戲鏡像與直播 – 可將手機畫面鏡像回電腦,方便遠端遊玩或進行直播分享,操作靈活便捷。
瞭解了DeskIn的強大優勢後,接下來我們將透過簡單明瞭的圖文步驟,手把手教您如何從頭開始設定,輕鬆實現用手機遠端暢玩電腦遊戲。
在本地裝置和遠端電腦上提前安裝 DeskIn ,如果是第一次使用,可以註冊一個免費帳號並登入。註冊帳號不僅能讓你的連線更加安全,還方便管理多台裝置,同時可統一管理付費方案,確保使用體驗更順暢。

打開本地設備上的DeskIn,在手機上輸入連線密碼。密碼屬於臨時密碼,也可以自行修改,比如可以自訂臨時密碼,改成簡單好記的密碼如1234567c。如果手機和電腦都登入了同一個帳號,則無需輸入密碼即可快速連線。

點擊「連線」,瞬間即可完成連線,快速進入遊戲體驗。

連線成功後,您可直接透過手機觸控螢幕,流暢操控電腦上的遊戲,隨時隨地暢玩 Steam 或 Epic 遊戲庫中的珍藏大作。無論是《楓之谷》、《天堂》、《GTA5》還是《魔物獵人》,都能在手機上享受完整操作體驗,讓遠端遊玩與本地遊戲一樣流暢。

Parsec 是目前市面上另一款優秀的遠端軟體之一。它採用先進的硬體加速編碼技術,能夠提供接近本地遊戲的流暢體驗,延遲低至個位數毫秒。相比其他遠端桌面軟體,Parsec 專為遊戲優化,支援 60FPS 高幀率串流,並且設定簡單易用。無論是 AAA 大作還是獨立遊戲,Parsec 都能讓您在手機上享受完整的 PC 遊戲體驗,真正實現隨時隨地遠端暢玩遊戲的自由。Parsec 行動端目前僅支援 Android安裝,不支援 iOS安裝,透過Android手機或外接適配Android的手把可以低延遲遠端遊玩 PC 遊戲,但不提供手機端自定義PC組合按鍵功能,操控靈活性上比 DeskIn還是差一些。所以接下來的方案主要演示電腦控制電腦遠端玩遊戲。
在兩台電腦上都下載並安裝 Parsec ,創建 Parsec 帳戶並在兩台設備上登入。

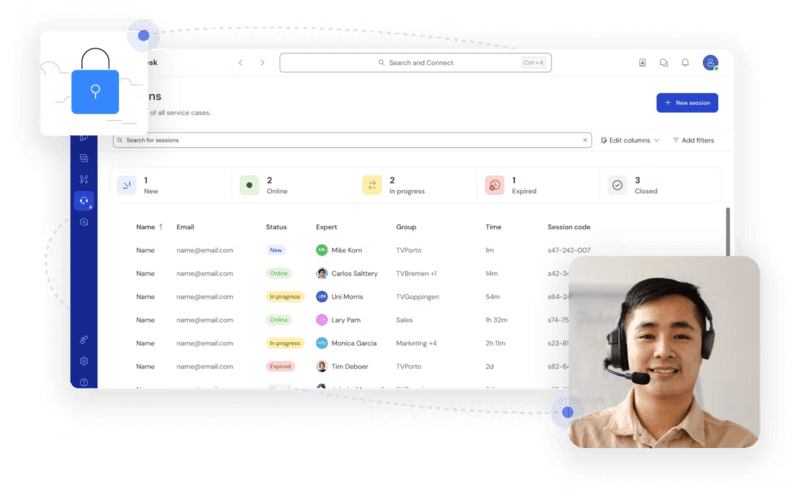
打开软件,登录账号。第一台电脑点击图中蓝色的「Share」,它会生成一个连接,将连接复制发给另一台电脑。
接下来是另一台电脑的操作,复制第一台电脑发来的链接,將連結貼在程式右下角方格中並按下「Join」即可。

連接成功後,你會看到桌面,可以直接操作遊戲,就像在本地玩一樣。
如果你沒有頂級電腦或希望減少硬體負擔,雲端遊戲服務是另一個理想選擇。透過 GeForce NOW、Xbox Cloud Gaming 或 Steam Cloud Play 等平台,遊戲運行在雲端伺服器上,手機、平板或輕薄筆電即可串流遊玩高畫質遊戲,完全不需擔心本地硬體性能。
操作簡單:只需安裝官方 App 或透過瀏覽器登入帳號,即可立即開始遊戲。
零距離限制:不論在家、通勤途中或朋友家,都能隨時暢玩 PC 或主機遊戲。
節省成本:不必購買高效能電腦或顯卡,即可體驗最新遊戲大作。
自動更新與存檔:遊戲在雲端運行,自動保持最新版本並同步進度,隨時隨地續玩。
缺點與限制:
遊戲庫受限,部分遊戲無法雲端遊玩。
多數平台需訂閱月費,長期成本不低。
對網路速度要求高,延遲與畫質受限。
無法自由安裝 MOD 或自訂設定。
某些服務在亞洲地區尚未正式開放。
若你希望「自由控制自己的電腦、暢玩所有遊戲、同時兼顧工作與娛樂」,DeskIn 是更靈活且零月費的理想選擇。
選擇你喜歡的雲端遊戲平台,創建帳號並安裝官方 App,或直接用瀏覽器登入。

在平台內選擇你想玩的遊戲,點擊「開始遊玩」即可,畫面會直接串流到你的裝置,手機或筆電也能流暢操作。
大多數雲端平台支援虛擬手把或外接控制器,讓你在手機或平板上也能享受完整遊戲操作體驗。
無論你是想在通勤途中續玩 Steam 遊戲,還是用筆電在咖啡廳體驗最新 AAA 大作,DeskIn都能讓你隨時隨地暢玩,不受距離與硬體限制。
手機遠端玩電腦遊戲需要在電腦安裝遠程軟體作為主機端,手機安裝對應 APP 作為客戶端,通過網路串流實現遊戲畫面和操控傳輸。最重要的是選擇一款合適的遠程軟體推薦,首推 DeskIn,專為遊戲優化,實現高畫質0延遲體驗,手機端操控響應極快,支援自定義觸控按鍵映射,讓手機也能流暢操作電腦遊戲。
iPhone 或 iPad 用戶需要注意平台支援。Parsec 不支援 iOS,無法在手機或平板上遠端遊玩,而 DeskIn 完全支援 iOS,低延遲、高畫質,並提供虛擬手把與按鍵映射功能,是 iOS 用戶的最佳選擇。
選擇遊戲遠程軟體需重點考慮延遲控制、畫質表現、網路適應性和硬體相容性等因素。強烈推薦 DeskIn,這款軟體專為遊戲場景打造,實現高畫質0延遲的卓越體驗,即使在複雜的網路環境下也能保持穩定連接,讓遠程遊戲如同本地操作般流暢。
遠端遊戲技術已經成熟到能提供真正流暢的跨裝置體驗。無論你想在通勤途中用手機繼續Steam進度,還是在朋友家用 Mac 暢玩Windows獨佔大作,本文介紹的 2 大方案都能滿足你的需求。
在眾多選擇中,DeskIn 無疑是最佳推薦。其專為遊戲打造的0延遲技術,配合高畫質4:4:4色彩還原和自定義遊戲按鍵功能,徹底解決了手機遠端玩電腦遊戲的核心痛點。相比其他方案,DeskIn 不僅設定簡單,更在複雜網路環境下保持卓越穩定性,讓每一次操作都如本地般即時響應。
現在就下載 DeskIn,開啟你的隨時隨地遊戲新體驗吧!不再受距離限制,讓高品質的PC遊戲庫真正為你所用,享受前所未有的遊戲自由度。

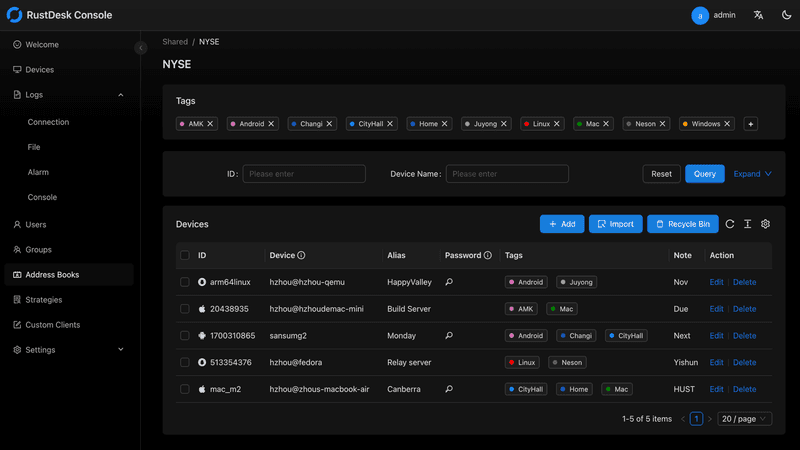
Top 6 RustDesk Alternative Tools for Faster, Easier Remote Access
Remote access should feel like flipping a light switch, not decoding a control panel. Yet many users exploring RustDesk eventually run into friction: connection IDs, server setup, or occasional lag. While RustDesk is powerful, it’s not always the easiest or smoothest option, especially for non-technical users.
That’s why more people are actively searching for a reliable RustDesk alternative that combines performance, simplicity, and flexibility. Whether you want a plug-and-play solution or something more advanced, this guide will help you find the best fit.
RustDesk stands out as a privacy-friendly, self-hosted remote desktop tool. However, real-world usage reveals a few common challenges:
Complicated setup for the RustDesk self-hosted environments
Manual connection steps requiring IDs and passwords
Occasional latency or unstable connections
Limited user-friendly features out of the box
For many users, especially those helping family or managing multiple devices, simplicity matters just as much as control.
When evaluating a RustDesk alternative, focus on these key factors:
Ease of use: Quick setup without technical overhead
Performance: Smooth, low-latency remote sessions
Compatibility: Support for Windows, macOS, Linux, and mobile
Security: Strong encryption and access controls
Flexibility: Options ranging from cloud-based to open source
The ideal tool strikes a balance between power and convenience, something many modern solutions now deliver better than traditional setups.
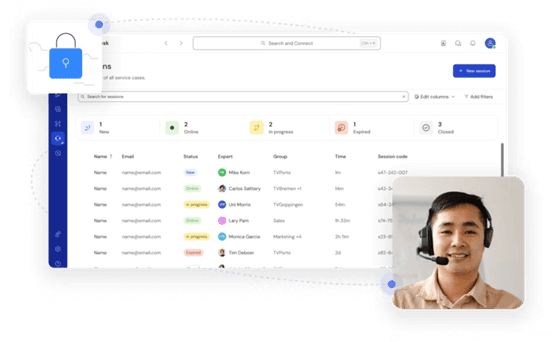
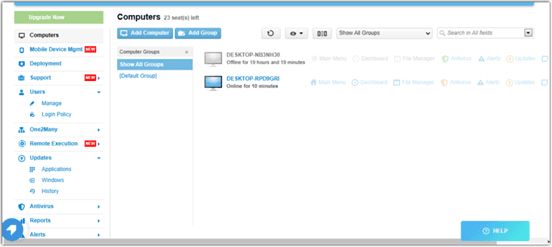
Here’s a quick breakdown of the top tools and where they shine:
DeskIn – Best all-in-one RustDesk alternative for performance and ease of use
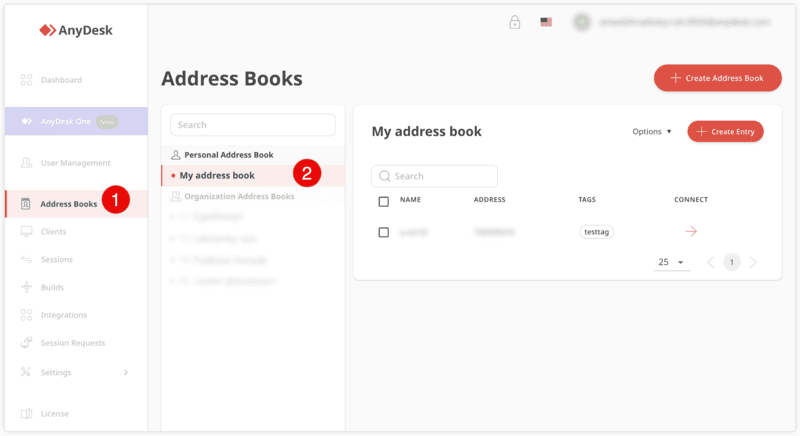
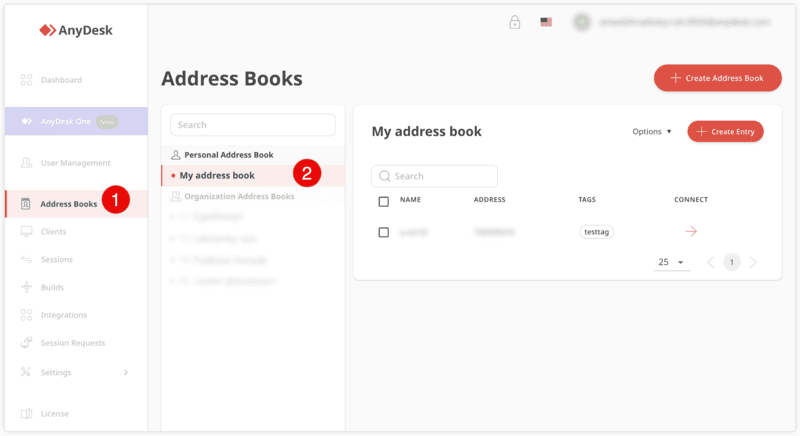
AnyDesk – Best lightweight tool for fast connections
TeamViewer – Best for enterprise-grade remote support
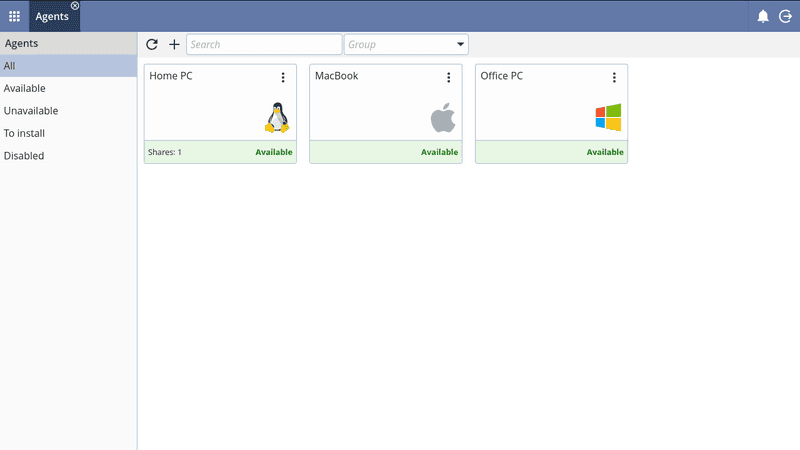
MeshCentral – Best open-source and self-hosted solution
DWService – Best free browser-based tool
Chrome Remote Desktop – Best simple, no-frills option
Ultra-low latency with smooth high-frame-rate streaming
No complex setup or server deployment required
Cross-platform including Rustdesk alternative for Android
Secure with encryption and device control features
Built-in file transfer and multi-device management
Smaller awareness than legacy competitors
Best for: Users who want a powerful yet simple remote desktop solution
DeskIn removes the friction that often comes with remote access tools. Instead of relying on IDs or manual configurations, it offers a streamlined connection experience that works right out of the box. This makes it especially valuable for users supporting non-technical family members or managing multiple remote devices.
Performance is where DeskIn truly distinguishes itself. Compared to RustDesk, which can sometimes struggle with latency, DeskIn delivers consistently smooth sessions with minimal lag. It also eliminates the need for self-hosting, making it a strong free RustDesk alternative option for users who want powerful features without the complexity.
For those exploring options beyond the RustDesk alternative GitHub projects, DeskIn provides a polished, ready-to-use experience that balances simplicity with professional-grade performance.
Lightweight and fast installation
Good performance on low bandwidth
Cross-platform support
Easy-to-use interface
Performance may drop during long sessions
File transfer can be inconsistent
Best for: Users needing quick and simple remote access
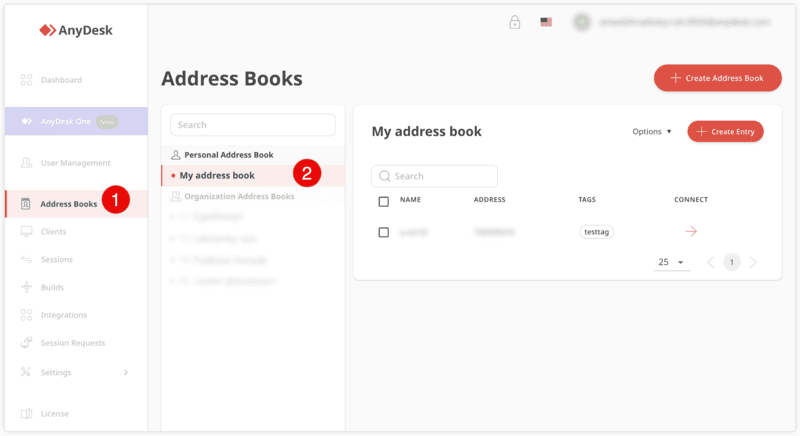
AnyDesk is often considered a natural step up from RustDesk for users who want something easier to deploy. It offers a lightweight application that connects quickly and performs well under normal conditions. This makes it suitable for quick troubleshooting or occasional remote access.
However, performance consistency can be an issue. Users frequently report lag or instability during extended sessions or when handling more demanding tasks. While AnyDesk is a solid option for basic needs, it may not fully satisfy users looking for a more robust, all-in-one solution.
👀 You may also be interested in: |
|---|
Enterprise-grade security with encryption and 2FA
Stable performance across global networks
Rich features like file transfer and session recording
Broad device compatibility
Expensive for commercial use
Free version has limitations
Heavier resource usage on some systems
Best for: Businesses and IT teams managing multiple endpoints
TeamViewer has long been a dominant player in the remote desktop space, offering a comprehensive suite of features designed for enterprise environments. It excels in reliability and global connectivity, making it a popular choice for IT support teams.
That said, its pricing model is a major drawback for many users. Frequent users may quickly encounter licensing restrictions, and costs can escalate for businesses. Additionally, its heavier footprint can impact performance on lower-end devices. DeskIn offers a more modern alternative by delivering similar performance and essential features without the same cost barriers. For users who want enterprise-level capabilities with better efficiency, it presents a compelling option.
👀 You may also be interested in: |
|---|
Fully RustDesk alternative open source solution
Web-based management dashboard
Supports multi-device environments
Strong customization and control
Complex setup and maintenance
Requires technical expertise
Best for: Advanced users needing a Rustdesk alternative self-hosted
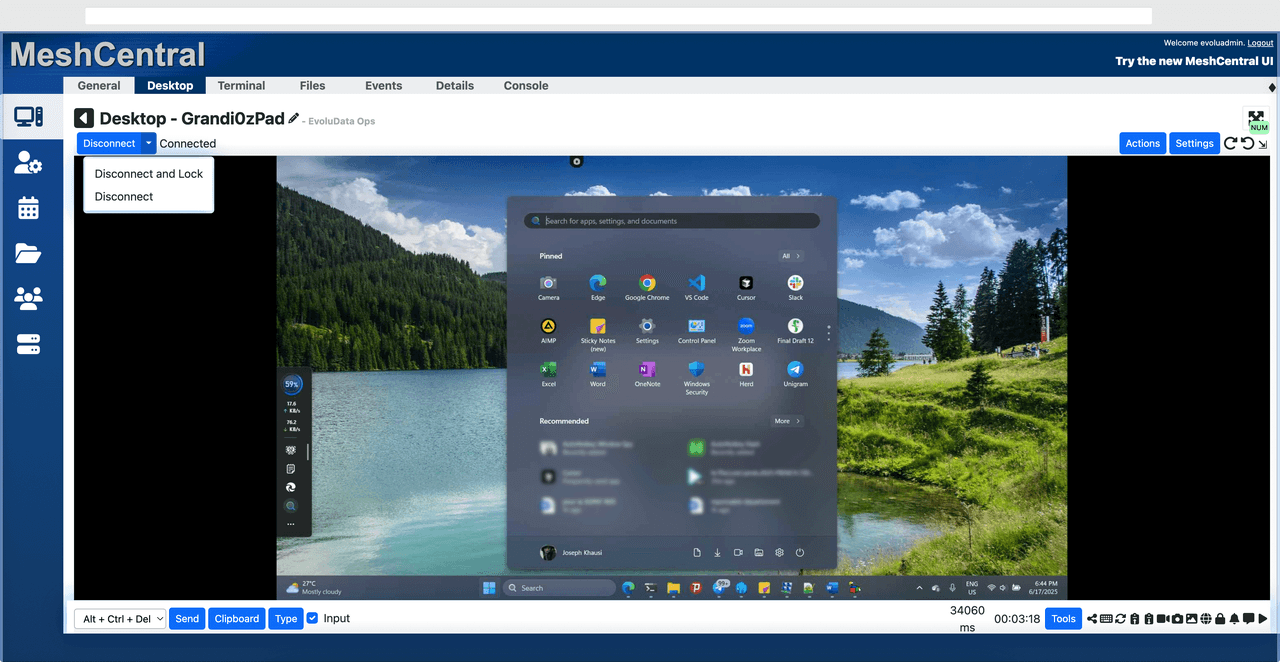
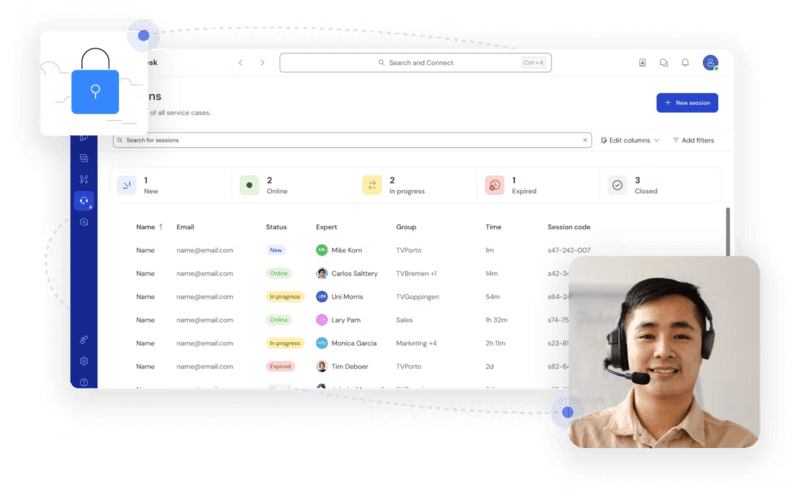
MeshCentral is a powerful open-source platform designed for users who want full control over their remote access infrastructure. It supports multiple devices and provides a centralized dashboard for management, making it attractive for IT professionals.
However, this flexibility comes with complexity. Setting up and maintaining a MeshCentral server requires technical knowledge, which can be a barrier for many users. Compared to this, DeskIn offers a much simpler deployment process while still delivering strong performance and security. For users who prioritize ease of use over full control, modern solutions like DeskIn provide a more accessible alternative.
Completely free
Browser-based access
Open-source foundation
Simple setup
Limited performance
Basic feature set
Best for: Users looking for a simple, free RustDesk alternative
DWService offers a browser-based approach to remote access with no heavy installation, making it convenient for quick connections in restricted environments. It supports both desktop access and file management across major platforms.
However, performance often feels sluggish, especially on demanding tasks, and features remain basic; lacking session recording, smooth multi-monitor support, or advanced security controls. While suitable for occasional personal use, it falls short for professional or high-performance scenarios.
Free and easy to use
Browser-based setup
Cross-platform compatibility
Very limited features
No advanced management or collaboration tools
Best for: Casual users needing basic remote access
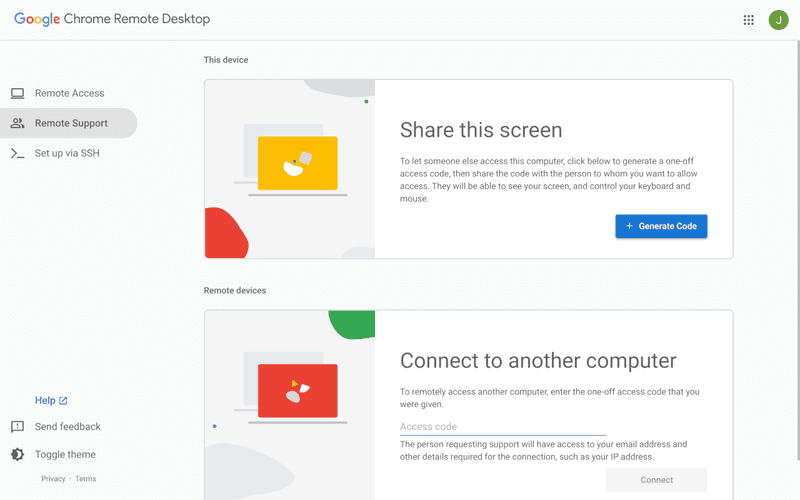
Chrome Remote Desktop is one of the simplest remote access tools available. It’s easy to set up and works across devices, making it a convenient choice for occasional use.
However, it lacks many essential features such as file transfer, session management, and advanced security controls. For users with more demanding needs, it quickly becomes insufficient. Compared to Chrome Remote Desktop, DeskIn provides a much more complete experience without sacrificing ease of use, making it a better long-term solution.
👀 You may also be interested in: |
|---|
RustDesk is powerful but can be difficult to set up and manage, especially with self-hosting. Many users prefer tools that offer similar performance without technical complexity. DeskIn simplifies remote access while maintaining strong performance and security.
Several tools qualify as a free RustDesk alternative, including DWService and Chrome Remote Desktop. However, DeskIn stands out by offering better performance and usability even in its free version.
Yes, tools like MeshCentral and DWService are considered RustDesk alternative open source options. They provide flexibility and control but often require technical expertise to set up and maintain.
Beginners should choose tools with a simple setup and intuitive interfaces. DeskIn is an excellent option because it removes the need for manual configuration while still delivering advanced features.
RustDesk is a powerful starting point, but it’s not always the easiest or most efficient tool for everyday use. From setup complexity to performance limitations, many users eventually look for a better RustDesk alternative.
Among all the options, DeskIn stands out as the most balanced solution. It combines speed, simplicity, and cross-platform support into one seamless experience. If you’re ready to move beyond technical friction and enjoy truly smooth remote access, DeskIn is a choice that simply works.

Top 7 RDP Alternative Tools for Faster, Safer Remote Access
Remote desktop access used to feel like a solid bridge. Now, for many users, traditional RDP feels more like a creaky rope ladder. With performance issues, security concerns, and limited cross-platform support, it's no surprise that more people are actively searching for a better RDP alternative that actually keeps up with modern workflows.
If you're managing multiple servers, working across devices, or just tired of unstable connections, this guide will walk you through the best tools worth switching to.
RDP (Remote Desktop Protocol) is a proprietary protocol developed by Microsoft that allows users to connect to another computer over a network. It's widely used for accessing Windows servers, virtual machines, and remote workstations.
While powerful in controlled environments, RDP is often tied to Windows systems and requires configuration like port forwarding or VPNs. Compared to newer tools, it can feel rigid and outdated.
You may also be interested in: |
|---|
RDP still works, but it comes with trade-offs that many users find frustrating:
Security risks if not properly configured
Complex setup for remote or external access
Limited cross-platform compatibility
Performance issues over unstable networks
Many IT teams are now actively replacing it, especially when looking for a Windows RDP client alternative or something that works seamlessly across macOS, Linux, and mobile devices. That's where modern Remote Desktop alternatives shine.
Choosing the right tool is like picking the right vehicle. Some are built for speed, others for heavy-duty enterprise work. Here's a quick snapshot:
DeskIn – Best all-in-one RDP alternative for performance and cross-platform use
TeamViewer – Best for enterprise remote support
AnyDesk – Best lightweight option for fast connections
RustDesk – Best Windows RDP alternative open-source solution
Remmina – Best RDP alternative for Linux users
Chrome Remote Desktop – Best simple browser-based tool
Splashtop – Best for high-performance business environments
Ultra-low latency with smooth high-frame-rate streaming
Works across Windows, macOS, Linux, iOS, and Android
Strong encryption and secure access controls
Built-in file transfer and multi-session support
Newer compared to legacy brands
Best for: Users who want a powerful, flexible RDP alternative
DeskIn feels less like remote access and more like teleportation for your desktop. Whether you're managing servers, supporting clients, or working remotely, it delivers consistently smooth performance without the usual lag spikes seen in traditional RDP setups.
Unlike many tools, DeskIn eliminates the need for complex configurations. You don't need to wrestle with firewalls or VPNs just to connect. It also works seamlessly across platforms, making it a strong alternative to Microsoft Remote Desktop for Mac and mobile users alike.
For teams juggling multiple systems, DeskIn provides a unified experience that replaces fragmented workflows. It's also a strong free RDP alternative option with premium-level capabilities, making it ideal for both individuals and businesses.
Enterprise-grade security and compliance
Extensive feature set including collaboration tools
Cross-platform compatibility
Reliable global performance
Expensive licensing
Can be overkill for individuals
Best for: Enterprises needing secure and scalable remote access
TeamViewer is a comprehensive remote desktop platform widely adopted by IT teams, support professionals, and enterprises. Its feature set extends far beyond simple screen sharing—it includes robust device management, remote printing, file transfer, session recording, and even augmented reality support for field service. TeamViewer's security architecture relies on AES‑256 encryption, two‑factor authentication, and whitelisting, making it suitable for organizations with strict compliance requirements. It runs on virtually every operating system and mobile platform.
The main trade‑off is its pricing: licenses are subscription‑based and can become expensive for small teams or individual users, especially as TeamViewer aggressively flags personal use as commercial, leading to session restrictions.
Fast and responsive
Lightweight installation
Works well on low bandwidth
Easy to use
File transfer can be inconsistent
Lag during longer sessions
Best for: Users needing quick, simple remote access
AnyDesk is a lightweight remote desktop application prized for its speed and efficiency, often recommended as a fast alternative to Microsoft's native Remote Desktop on Windows 10 and Android. It uses a proprietary video codec, DeskRT, to achieve low latency even on limited bandwidth, making it ideal for quick support sessions and accessing devices over mobile networks. The interface is clean and minimalist, with features like address book management, file transfer, and session recording available.
However, users frequently report instability during extended sessions; performance can degrade over time, and file transfers may slow considerably compared to competitors. While its free version is generous for personal use, professional users often find the performance ceiling limits its suitability for continuous, demanding workloads. DeskIn, by contrast, maintains consistent performance even during extended use, making it better suited for professional workloads.
You may also be interested in: |
|---|
Free and open-source
Self-hosting for full control
Strong privacy protection
Active community
Technical setup required
Limited user-friendly features
Best for: Developers and privacy-focused users
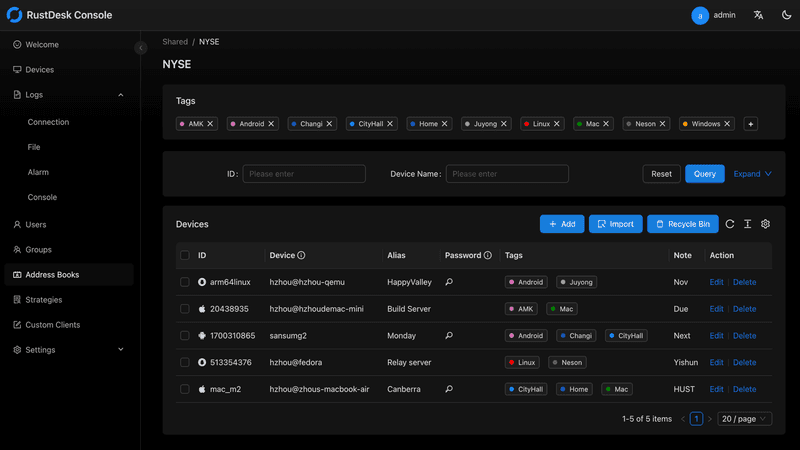
RustDesk has emerged as a leading open‑source remote desktop alternative, appealing to developers and organizations that require full control over their data. It allows users to self‑host the relay and rendezvous servers, meaning no third‑party infrastructure handles connection metadata. Built with Rust, it offers a modern codebase with cross‑platform clients (Windows, macOS, Linux, Android, iOS) and supports essential features such as file transfer, TCP tunneling, and customizable address books.
The major barrier is its complexity: deploying a self‑hosted environment requires technical expertise to configure firewalls, SSL certificates, and ongoing server maintenance. For those using the public relay, performance can be inconsistent depending on server load and geographic proximity.
You may also be interested in: Top RustDesk Alternatives for Better Performance, Security & Ease of Use |
|---|
Open-source and free
Supports multiple protocols including RDP and VNC
Lightweight and flexible
Native to Linux environments
Limited features compared to modern tools
UI can feel outdated
Best for: Linux users looking for a traditional RDP alternative Linux
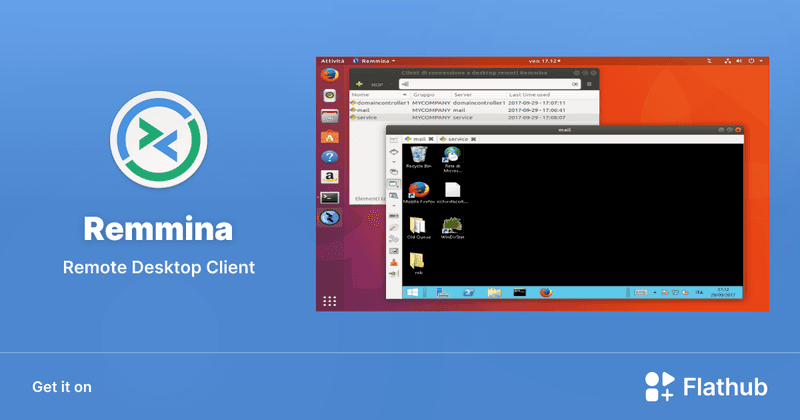
Remmina is a beloved open‑source remote desktop client for Linux, supporting multiple protocols (RDP, VNC, SSH, SPICE, and others) in a single unified interface. It is frequently chosen by system administrators and Linux enthusiasts who need a flexible, lightweight tool to manage diverse environments. Remmina offers tabbed sessions, quick‑connect profiles, and a plugin system that extends its capabilities.
However, its strength - protocol flexibility, also highlights its limitations. As a frontend client rather than a full remote access solution, it lacks features like unattended access, centralized account management, or robust session recording out of the box. Performance can vary by protocol, and the user experience lags behind more polished commercial tools, particularly for users seeking a plug‑and‑play setup.
Free and easy to use
Browser-based setup
Cross-platform access
Very limited features
No advanced management tools
Best for: Casual users needing basic remote access
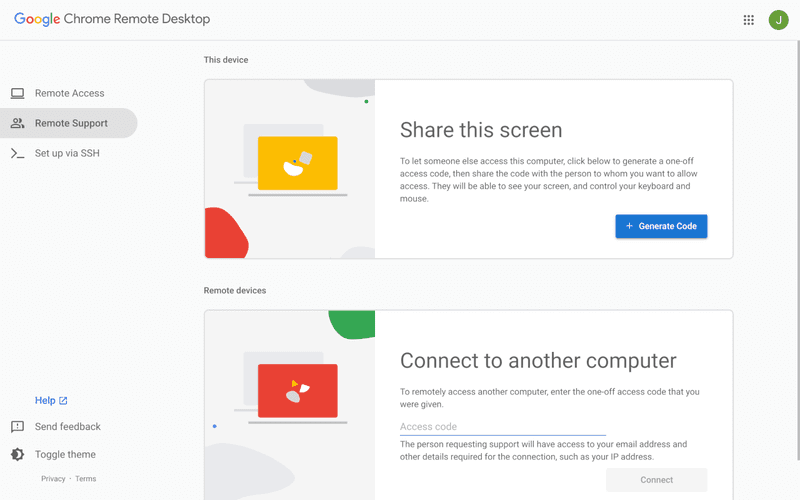
Chrome Remote Desktop is a free, browser‑based remote access tool from Google that requires nothing more than a Chrome browser and a Google account. It excels in simplicity: installation takes seconds, and connections are mediated through Google's infrastructure, eliminating complex firewall configurations. For occasional use—such as helping a family member or quickly accessing a home computer—it works reliably across Windows, macOS, Linux, and even ChromeOS.
The trade‑off is its minimal feature set. There is no native file transfer, multi‑session management, remote printing, or granular permission controls. Collaboration tools are absent, and the reliance on a Google account for authentication can be a limitation in professional environments. It remains a convenient entry‑level tool but struggles to meet the needs of power users or IT teams.
You may also be interested in: |
|---|
High-quality streaming performance
Strong security features
Good for business environments
Reliable connections
Subscription-based pricing
Limited free version
Best for: Businesses needing performance-focused remote access
Splashtop is a high‑performance remote desktop solution frequently adopted by creative professionals, educational institutions, and enterprises that prioritize fluid interaction. It delivers low‑latency streaming with support for high‑frame‑rate displays, making it suitable for video editing, CAD work, and other graphics‑intensive tasks. Splashtop offers a range of editions—from Business Access to SOS for on‑demand support—all of which include robust security (AES‑256, device authentication) and features like file transfer, remote printing, and multi‑monitor navigation. Its performance over local networks and the internet is consistently praised.
The primary drawback is cost: while competitive, the subscription model can accumulate quickly for users needing access to multiple devices or advanced features, especially when compared to similarly capable tools with more flexible pricing structures. DeskIn offers similar performance benefits with a more flexible pricing structure, making it a compelling alternative.
You may also be interested in: |
|---|
RDP can be difficult to configure, less secure if exposed, and limited outside Windows environments. Modern tools like DeskIn provide better performance, security, and ease of use.
The best RDP alternative depends on your needs, but DeskIn stands out for its balance of speed, security, and cross-platform compatibility.
Yes, several tools qualify as an RDP alternative free, including RustDesk and Chrome Remote Desktop. DeskIn also offers a free tier with advanced capabilities.
Microsoft is evolving its remote desktop ecosystem, but traditional RDP isn't disappearing overnight. However, many users are already transitioning to more modern solutions like DeskIn for better reliability and flexibility.
RDP has served its purpose, but the digital world has outgrown its limitations. Whether you need better performance, stronger security, or true cross-platform access, switching to a modern RDP alternative is no longer optional, it's inevitable.
Among all the options, DeskIn stands out as a future-ready solution. It combines speed, simplicity, and power into one seamless experience, helping you leave behind the friction of traditional remote desktop tools and step into something far more efficient.

Top 10 Splashtop Alternative Tools for Faster, More Reliable Remote Access (2026)
If your remote desktop tool has started to feel like a buffering video at the worst possible moment, you're not alone. Many users are actively searching for a better Splashtop alternative due to rising costs, laggy connections, and limited flexibility. Whether you're managing remote IT support or simply accessing your work computer from home, the right tool can turn frustration into seamless control. Let’s dive into the best options available today.
Before switching, it’s worth knowing what actually matters. A great remote desktop tool should offer:
Smooth performance with low latency and high frame rates
Strong security like AES-256 encryption and 2FA
Cross-platform compatibility (desktop + mobile)
Easy setup and intuitive interface
Transparent pricing without hidden increases
Stable unattended remote access
These factors define the best remote desktop experience in 2026.
Tool | Pros | Cons | Best For |
|---|---|---|---|
High performance, affordable, smooth | Newer brand | High-quality remote work | |
AnyDesk | Lightweight, fast | Security limits | Quick sessions |
TeamViewer | Secure, scalable | Expensive | Enterprises |
Chrome Remote Desktop | Free, simple
| Limited features | Personal use |
Zoho Assist | Clean UI, integrations | Stability issues | IT support |
RemotePC | Affordable | Performance inconsistency | SMBs |
RealVNC | Secure | Occasional disconnects | Secure access |
LogMeIn | Feature-rich | High cost | Enterprises |
ScreenConnect | Powerful | Complex setup | MSPs |
RustDesk | Open-source | Technical setup | Developers |
Up to 4K 60FPS/2K 240FPS ultra-smooth remote control
Low latency even across long distances
Competitive pricing with strong value
Cross-platform including mobile
Smaller brand awareness
Best for: Performance-driven users and remote professionals
DeskIn is designed for users who are tired of lag and blurry screens. It delivers a near-local experience, making it ideal for developers, designers, and remote teams who rely on precision and speed. Compared to many traditional tools, it feels significantly more responsive.
Beyond performance, DeskIn balances cost and capability extremely well. If you're looking for a free alternative to Splashtop or a scalable upgrade, it offers a compelling mix of speed, security, and usability. Many users consider it a strong case where DeskIn is better than Splashtop, especially when stability matters.
Very lightweight installation
Fast connections on low bandwidth
Easy to use interface
Limited advanced security features
Occasional connection instability
Best for: Quick remote support and simple workflows
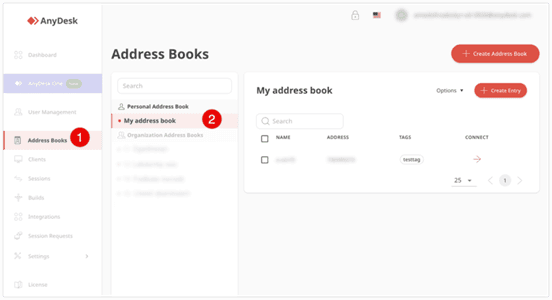
AnyDesk is frequently recommended as a Splashtop alternative thanks to its exceptional speed and minimal system footprint. The installer is just a few megabytes, and the application runs smoothly even on older hardware. It performs particularly well in low‑bandwidth environments, where its proprietary video codec maintains responsive connections during quick troubleshooting sessions.
That said, users who require consistently high frame rates, crisp visuals for design work, or advanced session management may find AnyDesk’s simplicity limiting. While it handles basic tasks admirably, power users often need more stability and richer feature sets.
You may also be interested in:
Strong security (AES-256, 2FA)
Wide device compatibility
Mature ecosystem and features
Reliable remote support tools
Expensive pricing plans
Can feel heavy for small teams
Best for: Enterprises and large organizations
TeamViewer has long been a dominant force in remote desktop software, trusted by IT departments and enterprises worldwide. Its comprehensive feature set includes remote support, meeting tools, file transfer, and even augmented‑reality assistance, all secured with AES‑256 encryption and two‑factor authentication.
However, this power comes at a price—literally. TeamViewer’s licensing model can be prohibitively expensive for smaller businesses or individual users. The interface, while feature‑rich, can also feel cluttered for those who simply need unattended access to a few computers.
You may also be interested in:
Completely free to use
Easy browser-based setup
Works across devices
Very limited features
Not suitable for business use
Best for: Individuals needing a free remote desktop
Chrome Remote Desktop is the ultimate choice for users seeking a straightforward, completely free remote access solution. Setup takes less than a minute: install the browser extension, authenticate with your Google account, and you can instantly access any computer from another device.
The trade‑off for this simplicity is a very limited feature set. There is no file transfer, multi‑monitor switching, remote printing, or session recording. Users who find themselves needing more than bare‑bones access will see a significant boost in efficiency and experience by upgrading to a dedicated tool like DeskIn, which retains ease of use while adding the features power users rely on.
You may also be interested in:
Intuitive interface
Good integrations with Zoho ecosystem
Cloud-based access
Occasional performance issues
Limited advanced features
Best for: IT helpdesk teams
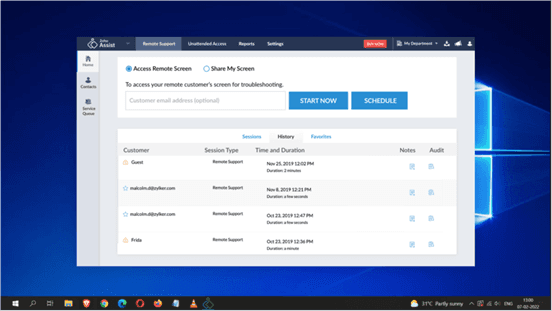
Zoho Assist delivers a clean, well‑organized remote support experience that integrates naturally with the broader Zoho ecosystem. Its dashboard is intuitive, making it easy for helpdesk teams to manage clients, schedule sessions, and generate reports. For organizations already using Zoho CRM or other Zoho applications, the seamless integration streamlines workflows and reduces the need to switch between different tools.
Despite its polished interface, performance consistency can be an issue, especially during file transfers or when connecting to machines with slower internet connections. The feature set, while sufficient for standard helpdesk operations, lacks some of the advanced controls that IT professionals expect for more complex troubleshooting.
Affordable pricing
Easy setup
Supports multiple devices
Performance can vary
Limited advanced capabilities
Best for: Small businesses and budget users
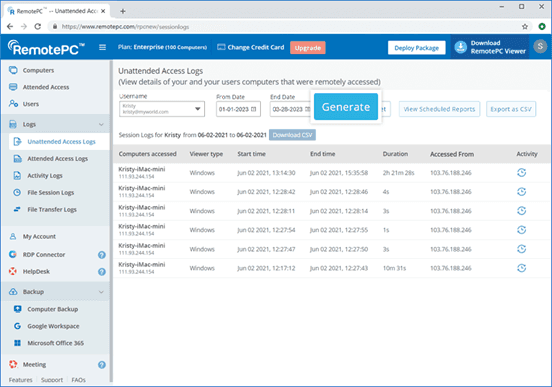
RemotePC positions itself as a budget‑friendly alternative for users who need basic remote access without a steep learning curve. Setup is straightforward, and the pricing structure is refreshingly simple—affordable plans that allow connection to multiple computers without hidden fees. It covers essential features like remote printing, file transfer, and even a simple chat function, making it a practical choice for small businesses and individual users.
However, performance can vary depending on network conditions and the specific devices being connected. Some users report occasional lag or reduced frame rates, which can become frustrating during extended sessions.
Strong encryption and security
Customisable setup
Reliable remote connections
Occasional login interruptions
Slight learning curve
Best for: Security-focused users
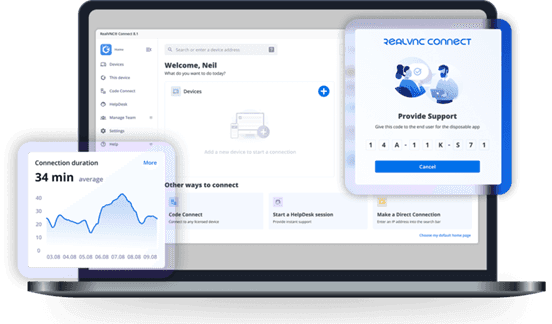
RealVNC has built a strong reputation for secure remote access. It uses robust encryption and offers granular permission controls, allowing administrators to tailor access levels for different users. The platform is highly customizable, supporting on‑premises deployments as well as cloud‑based options, which appeals to organizations with strict security requirements.
While security is clearly its strength, the user experience can sometimes feel less polished than newer competitors. Occasional login interruptions and a steeper configuration curve mean that getting the most out of RealVNC often requires technical expertise. For businesses that need both enterprise‑grade security and consistently high performance without complex setup, a more balanced solution, such as DeskIn, can deliver the best of both worlds, combining strong encryption with a streamlined, speed‑optimized experience.
Comprehensive feature set
Strong integrations
Good for collaboration
Reliable access
High pricing
Overkill for simple use cases
Best for: Enterprises needing all-in-one solutions
LogMeIn provides a comprehensive toolkit that extends far beyond simple remote desktop access. It includes robust file storage, collaboration features, and extensive integration options, making it well‑suited for enterprises that want an all‑in‑one remote work platform. The service is known for its reliability and strong customer support, which can be critical for large organizations managing hundreds or thousands of endpoints.
The main drawback is the cost. LogMeIn’s pricing plans are among the highest in the industry, and the feature set can be overwhelming for users who only need occasional remote access. Many of its advanced capabilities go unused by smaller teams, making it difficult to justify the expense.
Highly customizable
Remote support features
Multi-session support
Complex setup
Difficult to manage at scale
Best for: MSPs and IT teams
ScreenConnect (now part of ConnectWise) is a powerful, highly customizable remote support platform built with IT professionals and managed service providers in mind. It excels at multi‑session management, allowing technicians to handle several concurrent connections from a single interface. The level of granular control, over permissions, session recording, and even the appearance of the client UI, makes it a favorite among those who need to tailor the software to specific operational workflows.
However, this flexibility comes with a steep learning curve. Initial setup and ongoing management can be complex, especially for smaller teams without dedicated IT administration. For teams seeking a powerful yet approachable solution, DeskIn offers a streamlined alternative that delivers professional‑grade reliability and speed without the administrative overhead.
Free and open-source
Self-hosting options
Strong privacy control
Requires technical setup
Limited support
Best for: Developers and privacy-focused users
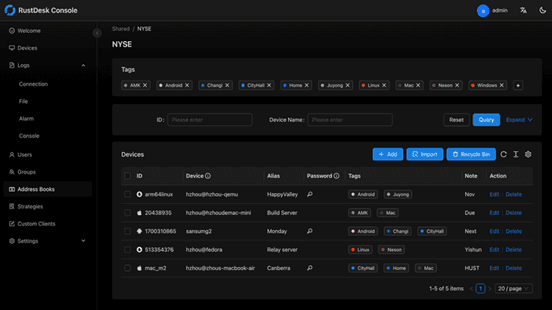
RustDesk appeals to developers and privacy‑conscious users who want full control over their remote access infrastructure. As an open‑source solution, it allows self‑hosting on private servers, ensuring that no session data ever passes through third‑party servers. This transparency and autonomy are highly valued by organizations with strict data sovereignty requirements or those simply wishing to avoid vendor lock‑in.
The flip side is that RustDesk requires technical expertise to deploy and maintain. Users must manage their own servers, handle updates, and troubleshoot connection issues without dedicated commercial support. While the core software is free, the total cost of ownership in time and resources can be significant.
You may also be interested in:
DeskIn is one of the strongest options due to its balance of performance, pricing, and usability. TeamViewer and AnyDesk are also popular choices.
Yes, Chrome Remote Desktop and RustDesk are free options. DeskIn also offers a competitive free plan with better performance.
The best remote desktop tools combine speed, security, and ease of use. DeskIn stands out for performance, while TeamViewer excels in enterprise environments.
Yes, most tools support mobile, making them suitable as a Splashtop alternative for Android or a Splashtop alternative for iPad.
Many users cite high Splashtop pricing, lag issues, and limited scalability as reasons to explore alternatives.
Finding the right Splashtop alternative is less about replacing a tool and more about upgrading your workflow. While options like AnyDesk and TeamViewer each have their strengths, DeskIn stands out by combining high performance, smooth visuals, and cost efficiency in one package. If you want a remote desktop experience that feels fast, stable, and future-ready, DeskIn is easily one of the smartest choices you can make today.

Top 6 RustDesk Alternative Tools for Faster, Easier Remote Access
Remote access should feel like flipping a light switch, not decoding a control panel. Yet many users exploring RustDesk eventually run into friction: connection IDs, server setup, or occasional lag. While RustDesk is powerful, it’s not always the easiest or smoothest option, especially for non-technical users.
That’s why more people are actively searching for a reliable RustDesk alternative that combines performance, simplicity, and flexibility. Whether you want a plug-and-play solution or something more advanced, this guide will help you find the best fit.
RustDesk stands out as a privacy-friendly, self-hosted remote desktop tool. However, real-world usage reveals a few common challenges:
Complicated setup for the RustDesk self-hosted environments
Manual connection steps requiring IDs and passwords
Occasional latency or unstable connections
Limited user-friendly features out of the box
For many users, especially those helping family or managing multiple devices, simplicity matters just as much as control.
When evaluating a RustDesk alternative, focus on these key factors:
Ease of use: Quick setup without technical overhead
Performance: Smooth, low-latency remote sessions
Compatibility: Support for Windows, macOS, Linux, and mobile
Security: Strong encryption and access controls
Flexibility: Options ranging from cloud-based to open source
The ideal tool strikes a balance between power and convenience, something many modern solutions now deliver better than traditional setups.
Here’s a quick breakdown of the top tools and where they shine:
DeskIn – Best all-in-one RustDesk alternative for performance and ease of use
AnyDesk – Best lightweight tool for fast connections
TeamViewer – Best for enterprise-grade remote support
MeshCentral – Best open-source and self-hosted solution
DWService – Best free browser-based tool
Chrome Remote Desktop – Best simple, no-frills option
Ultra-low latency with smooth high-frame-rate streaming
No complex setup or server deployment required
Cross-platform including Rustdesk alternative for Android
Secure with encryption and device control features
Built-in file transfer and multi-device management
Smaller awareness than legacy competitors
Best for: Users who want a powerful yet simple remote desktop solution
DeskIn removes the friction that often comes with remote access tools. Instead of relying on IDs or manual configurations, it offers a streamlined connection experience that works right out of the box. This makes it especially valuable for users supporting non-technical family members or managing multiple remote devices.
Performance is where DeskIn truly distinguishes itself. Compared to RustDesk, which can sometimes struggle with latency, DeskIn delivers consistently smooth sessions with minimal lag. It also eliminates the need for self-hosting, making it a strong free RustDesk alternative option for users who want powerful features without the complexity.
For those exploring options beyond the RustDesk alternative GitHub projects, DeskIn provides a polished, ready-to-use experience that balances simplicity with professional-grade performance.
Lightweight and fast installation
Good performance on low bandwidth
Cross-platform support
Easy-to-use interface
Performance may drop during long sessions
File transfer can be inconsistent
Best for: Users needing quick and simple remote access
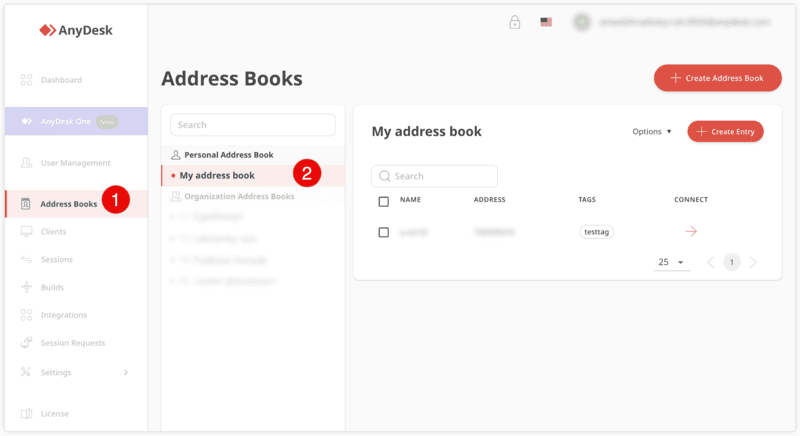
AnyDesk is often considered a natural step up from RustDesk for users who want something easier to deploy. It offers a lightweight application that connects quickly and performs well under normal conditions. This makes it suitable for quick troubleshooting or occasional remote access.
However, performance consistency can be an issue. Users frequently report lag or instability during extended sessions or when handling more demanding tasks. While AnyDesk is a solid option for basic needs, it may not fully satisfy users looking for a more robust, all-in-one solution.
👀 You may also be interested in: |
|---|
Enterprise-grade security with encryption and 2FA
Stable performance across global networks
Rich features like file transfer and session recording
Broad device compatibility
Expensive for commercial use
Free version has limitations
Heavier resource usage on some systems
Best for: Businesses and IT teams managing multiple endpoints
TeamViewer has long been a dominant player in the remote desktop space, offering a comprehensive suite of features designed for enterprise environments. It excels in reliability and global connectivity, making it a popular choice for IT support teams.
That said, its pricing model is a major drawback for many users. Frequent users may quickly encounter licensing restrictions, and costs can escalate for businesses. Additionally, its heavier footprint can impact performance on lower-end devices. DeskIn offers a more modern alternative by delivering similar performance and essential features without the same cost barriers. For users who want enterprise-level capabilities with better efficiency, it presents a compelling option.
👀 You may also be interested in: |
|---|
Fully RustDesk alternative open source solution
Web-based management dashboard
Supports multi-device environments
Strong customization and control
Complex setup and maintenance
Requires technical expertise
Best for: Advanced users needing a Rustdesk alternative self-hosted
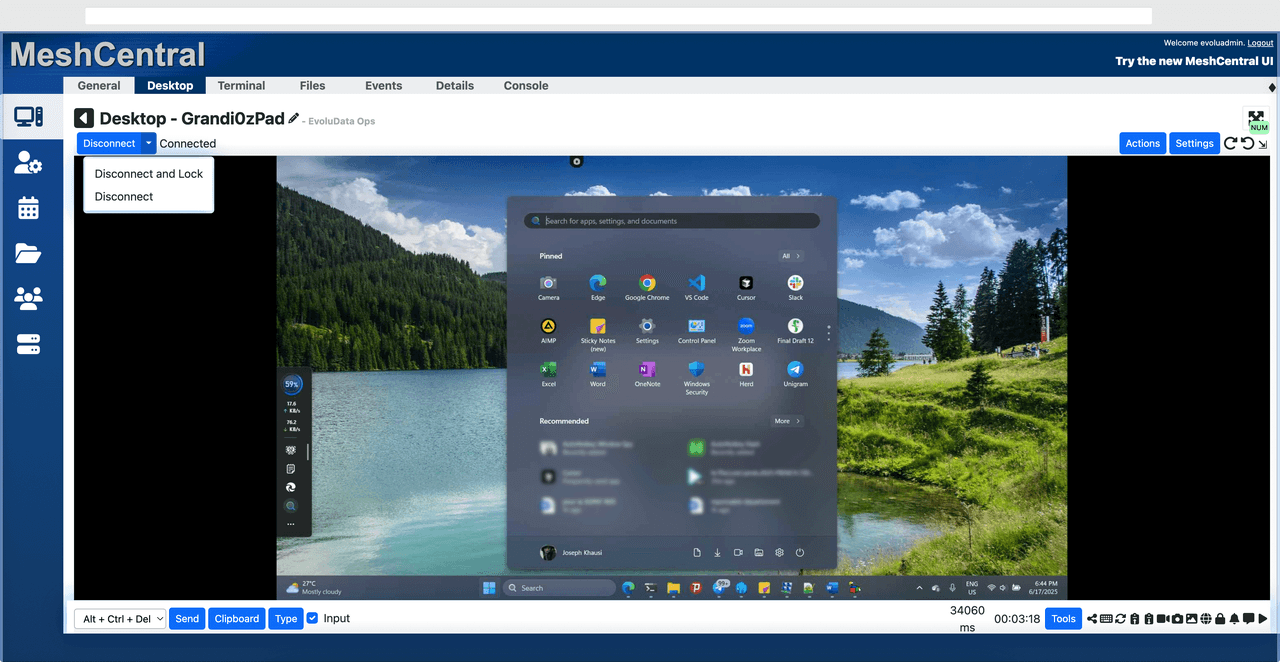
MeshCentral is a powerful open-source platform designed for users who want full control over their remote access infrastructure. It supports multiple devices and provides a centralized dashboard for management, making it attractive for IT professionals.
However, this flexibility comes with complexity. Setting up and maintaining a MeshCentral server requires technical knowledge, which can be a barrier for many users. Compared to this, DeskIn offers a much simpler deployment process while still delivering strong performance and security. For users who prioritize ease of use over full control, modern solutions like DeskIn provide a more accessible alternative.
Completely free
Browser-based access
Open-source foundation
Simple setup
Limited performance
Basic feature set
Best for: Users looking for a simple, free RustDesk alternative
DWService offers a browser-based approach to remote access with no heavy installation, making it convenient for quick connections in restricted environments. It supports both desktop access and file management across major platforms.
However, performance often feels sluggish, especially on demanding tasks, and features remain basic; lacking session recording, smooth multi-monitor support, or advanced security controls. While suitable for occasional personal use, it falls short for professional or high-performance scenarios.
Free and easy to use
Browser-based setup
Cross-platform compatibility
Very limited features
No advanced management or collaboration tools
Best for: Casual users needing basic remote access
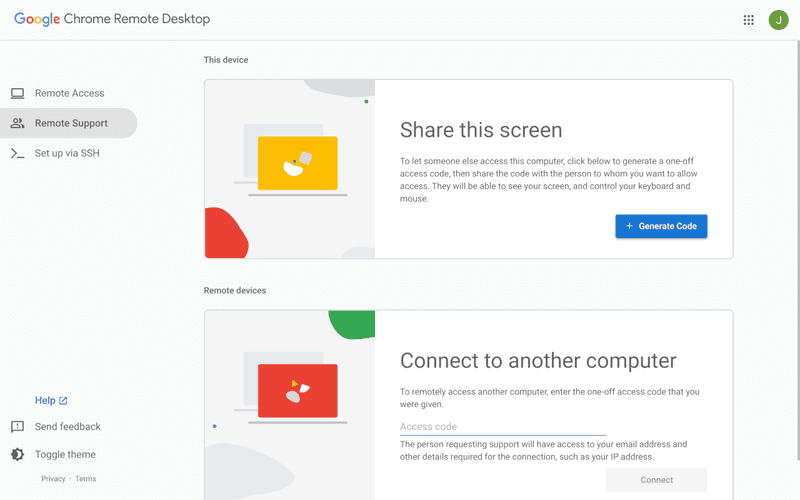
Chrome Remote Desktop is one of the simplest remote access tools available. It’s easy to set up and works across devices, making it a convenient choice for occasional use.
However, it lacks many essential features such as file transfer, session management, and advanced security controls. For users with more demanding needs, it quickly becomes insufficient. Compared to Chrome Remote Desktop, DeskIn provides a much more complete experience without sacrificing ease of use, making it a better long-term solution.
👀 You may also be interested in: |
|---|
RustDesk is powerful but can be difficult to set up and manage, especially with self-hosting. Many users prefer tools that offer similar performance without technical complexity. DeskIn simplifies remote access while maintaining strong performance and security.
Several tools qualify as a free RustDesk alternative, including DWService and Chrome Remote Desktop. However, DeskIn stands out by offering better performance and usability even in its free version.
Yes, tools like MeshCentral and DWService are considered RustDesk alternative open source options. They provide flexibility and control but often require technical expertise to set up and maintain.
Beginners should choose tools with a simple setup and intuitive interfaces. DeskIn is an excellent option because it removes the need for manual configuration while still delivering advanced features.
RustDesk is a powerful starting point, but it’s not always the easiest or most efficient tool for everyday use. From setup complexity to performance limitations, many users eventually look for a better RustDesk alternative.
Among all the options, DeskIn stands out as the most balanced solution. It combines speed, simplicity, and cross-platform support into one seamless experience. If you’re ready to move beyond technical friction and enjoy truly smooth remote access, DeskIn is a choice that simply works.

Top 7 RDP Alternative Tools for Faster, Safer Remote Access
Remote desktop access used to feel like a solid bridge. Now, for many users, traditional RDP feels more like a creaky rope ladder. With performance issues, security concerns, and limited cross-platform support, it's no surprise that more people are actively searching for a better RDP alternative that actually keeps up with modern workflows.
If you're managing multiple servers, working across devices, or just tired of unstable connections, this guide will walk you through the best tools worth switching to.
RDP (Remote Desktop Protocol) is a proprietary protocol developed by Microsoft that allows users to connect to another computer over a network. It's widely used for accessing Windows servers, virtual machines, and remote workstations.
While powerful in controlled environments, RDP is often tied to Windows systems and requires configuration like port forwarding or VPNs. Compared to newer tools, it can feel rigid and outdated.
You may also be interested in: |
|---|
RDP still works, but it comes with trade-offs that many users find frustrating:
Security risks if not properly configured
Complex setup for remote or external access
Limited cross-platform compatibility
Performance issues over unstable networks
Many IT teams are now actively replacing it, especially when looking for a Windows RDP client alternative or something that works seamlessly across macOS, Linux, and mobile devices. That's where modern Remote Desktop alternatives shine.
Choosing the right tool is like picking the right vehicle. Some are built for speed, others for heavy-duty enterprise work. Here's a quick snapshot:
DeskIn – Best all-in-one RDP alternative for performance and cross-platform use
TeamViewer – Best for enterprise remote support
AnyDesk – Best lightweight option for fast connections
RustDesk – Best Windows RDP alternative open-source solution
Remmina – Best RDP alternative for Linux users
Chrome Remote Desktop – Best simple browser-based tool
Splashtop – Best for high-performance business environments
Ultra-low latency with smooth high-frame-rate streaming
Works across Windows, macOS, Linux, iOS, and Android
Strong encryption and secure access controls
Built-in file transfer and multi-session support
Newer compared to legacy brands
Best for: Users who want a powerful, flexible RDP alternative
DeskIn feels less like remote access and more like teleportation for your desktop. Whether you're managing servers, supporting clients, or working remotely, it delivers consistently smooth performance without the usual lag spikes seen in traditional RDP setups.
Unlike many tools, DeskIn eliminates the need for complex configurations. You don't need to wrestle with firewalls or VPNs just to connect. It also works seamlessly across platforms, making it a strong alternative to Microsoft Remote Desktop for Mac and mobile users alike.
For teams juggling multiple systems, DeskIn provides a unified experience that replaces fragmented workflows. It's also a strong free RDP alternative option with premium-level capabilities, making it ideal for both individuals and businesses.
Enterprise-grade security and compliance
Extensive feature set including collaboration tools
Cross-platform compatibility
Reliable global performance
Expensive licensing
Can be overkill for individuals
Best for: Enterprises needing secure and scalable remote access
TeamViewer is a comprehensive remote desktop platform widely adopted by IT teams, support professionals, and enterprises. Its feature set extends far beyond simple screen sharing—it includes robust device management, remote printing, file transfer, session recording, and even augmented reality support for field service. TeamViewer's security architecture relies on AES‑256 encryption, two‑factor authentication, and whitelisting, making it suitable for organizations with strict compliance requirements. It runs on virtually every operating system and mobile platform.
The main trade‑off is its pricing: licenses are subscription‑based and can become expensive for small teams or individual users, especially as TeamViewer aggressively flags personal use as commercial, leading to session restrictions.
Fast and responsive
Lightweight installation
Works well on low bandwidth
Easy to use
File transfer can be inconsistent
Lag during longer sessions
Best for: Users needing quick, simple remote access
AnyDesk is a lightweight remote desktop application prized for its speed and efficiency, often recommended as a fast alternative to Microsoft's native Remote Desktop on Windows 10 and Android. It uses a proprietary video codec, DeskRT, to achieve low latency even on limited bandwidth, making it ideal for quick support sessions and accessing devices over mobile networks. The interface is clean and minimalist, with features like address book management, file transfer, and session recording available.
However, users frequently report instability during extended sessions; performance can degrade over time, and file transfers may slow considerably compared to competitors. While its free version is generous for personal use, professional users often find the performance ceiling limits its suitability for continuous, demanding workloads. DeskIn, by contrast, maintains consistent performance even during extended use, making it better suited for professional workloads.
You may also be interested in: |
|---|
Free and open-source
Self-hosting for full control
Strong privacy protection
Active community
Technical setup required
Limited user-friendly features
Best for: Developers and privacy-focused users
RustDesk has emerged as a leading open‑source remote desktop alternative, appealing to developers and organizations that require full control over their data. It allows users to self‑host the relay and rendezvous servers, meaning no third‑party infrastructure handles connection metadata. Built with Rust, it offers a modern codebase with cross‑platform clients (Windows, macOS, Linux, Android, iOS) and supports essential features such as file transfer, TCP tunneling, and customizable address books.
The major barrier is its complexity: deploying a self‑hosted environment requires technical expertise to configure firewalls, SSL certificates, and ongoing server maintenance. For those using the public relay, performance can be inconsistent depending on server load and geographic proximity.
You may also be interested in: Top RustDesk Alternatives for Better Performance, Security & Ease of Use |
|---|
Open-source and free
Supports multiple protocols including RDP and VNC
Lightweight and flexible
Native to Linux environments
Limited features compared to modern tools
UI can feel outdated
Best for: Linux users looking for a traditional RDP alternative Linux
Remmina is a beloved open‑source remote desktop client for Linux, supporting multiple protocols (RDP, VNC, SSH, SPICE, and others) in a single unified interface. It is frequently chosen by system administrators and Linux enthusiasts who need a flexible, lightweight tool to manage diverse environments. Remmina offers tabbed sessions, quick‑connect profiles, and a plugin system that extends its capabilities.
However, its strength - protocol flexibility, also highlights its limitations. As a frontend client rather than a full remote access solution, it lacks features like unattended access, centralized account management, or robust session recording out of the box. Performance can vary by protocol, and the user experience lags behind more polished commercial tools, particularly for users seeking a plug‑and‑play setup.
Free and easy to use
Browser-based setup
Cross-platform access
Very limited features
No advanced management tools
Best for: Casual users needing basic remote access
Chrome Remote Desktop is a free, browser‑based remote access tool from Google that requires nothing more than a Chrome browser and a Google account. It excels in simplicity: installation takes seconds, and connections are mediated through Google's infrastructure, eliminating complex firewall configurations. For occasional use—such as helping a family member or quickly accessing a home computer—it works reliably across Windows, macOS, Linux, and even ChromeOS.
The trade‑off is its minimal feature set. There is no native file transfer, multi‑session management, remote printing, or granular permission controls. Collaboration tools are absent, and the reliance on a Google account for authentication can be a limitation in professional environments. It remains a convenient entry‑level tool but struggles to meet the needs of power users or IT teams.
You may also be interested in: |
|---|
High-quality streaming performance
Strong security features
Good for business environments
Reliable connections
Subscription-based pricing
Limited free version
Best for: Businesses needing performance-focused remote access
Splashtop is a high‑performance remote desktop solution frequently adopted by creative professionals, educational institutions, and enterprises that prioritize fluid interaction. It delivers low‑latency streaming with support for high‑frame‑rate displays, making it suitable for video editing, CAD work, and other graphics‑intensive tasks. Splashtop offers a range of editions—from Business Access to SOS for on‑demand support—all of which include robust security (AES‑256, device authentication) and features like file transfer, remote printing, and multi‑monitor navigation. Its performance over local networks and the internet is consistently praised.
The primary drawback is cost: while competitive, the subscription model can accumulate quickly for users needing access to multiple devices or advanced features, especially when compared to similarly capable tools with more flexible pricing structures. DeskIn offers similar performance benefits with a more flexible pricing structure, making it a compelling alternative.
You may also be interested in: |
|---|
RDP can be difficult to configure, less secure if exposed, and limited outside Windows environments. Modern tools like DeskIn provide better performance, security, and ease of use.
The best RDP alternative depends on your needs, but DeskIn stands out for its balance of speed, security, and cross-platform compatibility.
Yes, several tools qualify as an RDP alternative free, including RustDesk and Chrome Remote Desktop. DeskIn also offers a free tier with advanced capabilities.
Microsoft is evolving its remote desktop ecosystem, but traditional RDP isn't disappearing overnight. However, many users are already transitioning to more modern solutions like DeskIn for better reliability and flexibility.
RDP has served its purpose, but the digital world has outgrown its limitations. Whether you need better performance, stronger security, or true cross-platform access, switching to a modern RDP alternative is no longer optional, it's inevitable.
Among all the options, DeskIn stands out as a future-ready solution. It combines speed, simplicity, and power into one seamless experience, helping you leave behind the friction of traditional remote desktop tools and step into something far more efficient.
聯絡我們
電子郵件: support@deskin.io
總部: 991D Alexandra Road #02-17, Singapore 119972
聯絡我們
電子郵件: support@deskin.io
總部: 991D Alexandra Road #02-17, Singapore 119972
聯絡我們
support@deskin.io
991D Alexandra Road #02-17, Singapore 119972
年付低至
2.1 折
!4K60FPS 順暢辦公 + 遊戲,
錯過等1年!
低至
2.1 折
解鎖極致遠端體驗,
錯過等1年!
年付低至
2.1 折
!4K60FPS 順暢辦公 + 遊戲,
錯過等1年!