Công nghệ
Công nghệ
/
5 phút
/
5 phút
GA
Đã cập nhật
Đã cập nhật
Đã cập nhật
Làm việc từ xa thật tuyệt vời cho đến khi nó không còn tuyệt nữa.
Bạn có những người đang thiết kế trên Figma từ bãi biển, chốt giao dịch qua Zoom trong quán cà phê, hoặc viết code khi đang chờ ở sân bay. Nó nhanh, linh hoạt và có chút kỳ diệu. Nhưng đây là điểm mấu chốt: đằng sau mỗi cú nhấp chuột, mỗi tệp được chia sẻ, mỗi lần đăng nhập từ xa, có một thứ âm thầm giữ mọi thứ vận hành — thông tin xác thực.
Và nếu người không phù hợp nắm được những thông tin xác thực đó, mọi thứ có thể xấu đi rất nhanh.

Đó là lý do vì sao quản lý thông tin xác thực cực kỳ quan trọng, hơn bao giờ hết. Không chỉ là ghi lại mật khẩu trong một kho an toàn, mà là kiểm soát ai được truy cập vào cái gì và khi nào. Từ bảo vệ thông tin xác thực của công ty đến xoay vòng thông tin xác thực bảo mật và thiết lập MFA, đó là cách để bạn đảm bảo cánh cửa số luôn được khóa, và chỉ đúng người mới có chìa khóa.
May mắn là, các công cụ như DeskIn giúp bảo mật truy cập từ xa dễ dàng hơn rất nhiều (và thông minh hơn). Trong bài viết này, chúng tôi sẽ phân tích quản lý thông tin xác thực là gì, cách nó hoạt động, và cách bạn có thể dùng nó để khóa chặt hệ thống mà không khóa luôn cả đội ngũ của mình.
Hãy bắt đầu.
Mỗi mật khẩu, mã API, khóa SSH, chứng chỉ, hay quét vân tay về cơ bản đều là một chiếc chìa khóa cho thứ gì đó quan trọng trong thế giới số của công ty bạn. Và thành thật mà nói, theo dõi vài chiếc chìa khóa thì dễ, nhưng hàng trăm hoặc hàng nghìn chiếc thì đó là công thức cho việc mất đăng nhập, chia sẻ quá mức ngoài ý muốn, hoặc tệ hơn, vi phạm bảo mật.
Đây là lúc quản lý thông tin xác thực phát huy tác dụng. Hệ thống giữ tất cả những chìa khóa đó sẽ khóa chúng an toàn và chỉ cấp cho đúng người vào đúng thời điểm.
Một cách hình dung tốt hơn về quản lý thông tin xác thực không phải là một danh sách mật khẩu bụi bặm, mà là một “nhân viên bảo vệ” ảo biết ai nên và không nên có quyền truy cập, đảm bảo đúng người được vào và ngăn người không phù hợp ở ngoài.
Khi được triển khai đúng cách, quản lý thông tin xác thực giúp đội ngũ của bạn làm việc thông suốt đồng thời ngăn hacker và những “vị khách” không mong muốn xâm nhập.
Một thiết lập quản lý thông tin xác thực đúng chuẩn hoạt động như một đội bảo mật toàn thời gian cho các đăng nhập của bạn. Đây là những gì nó làm:
Lưu trữ an toàn – Mã hóa thông tin xác thực và giữ chúng trong kho bảo mật, tránh xa giấy nhớ dán hoặc tệp không được bảo vệ.
Truy xuất an toàn – Chỉ cung cấp thông tin xác thực cho người dùng được ủy quyền, không hiển thị dạng văn bản thuần hoặc gây rủi ro rò rỉ do sao chép-dán.
Cập nhật tự động – Xoay vòng mật khẩu, làm mới mã token và cập nhật chứng chỉ để ngăn hết hạn/bị khai thác.
Thu hồi tức thì – Cắt quyền truy cập ngay khi ai đó rời nhóm hoặc đổi vai trò, không để lại “cửa sau” nào mở.
Quản lý thông tin xác thực là nền tảng của xác thực an toàn và quản lý danh tính; thiếu nó, mọi biện pháp bảo mật khác đều trở nên yếu hơn.
Xác thực an toàn – Xác nhận danh tính từng người dùng, thêm các lớp bảo vệ như MFA, và chặn các thói quen rủi ro như tái sử dụng thông tin xác thực.
Quản lý danh tính – Gắn mỗi thông tin xác thực với một vai trò hoặc quyền cụ thể để người dùng chỉ được truy cập những gì họ thực sự cần, đồng thời giữ lại dấu vết rõ ràng, có thể kiểm toán cho mọi hành động.
Tóm lại, quản lý thông tin xác thực không chỉ bảo vệ mật khẩu; nó còn giúp bảo vệ các hoạt động số cốt lõi của doanh nghiệp bạn.

Có nhiều cấp độ thông tin xác thực là có lý do. Mỗi loại phục vụ một mục đích khác nhau, và điều quan trọng là phải hiểu cách làm việc với chúng để giữ an toàn cho làm việc từ xa. Một hệ thống quản lý thông tin xác thực mạnh không chỉ lưu trữ các thông tin này; nó biết dùng tổ hợp nào, khi nào và ở đâu. Vì vậy, dưới đây là các loại chính và lý do chúng quan trọng.
Loại thông tin xác thực kinh điển, đơn giản, quen thuộc, và không may là vẫn là mục tiêu ưa thích của kẻ tấn công. Mật khẩu yếu hoặc dùng lại là lời mời công khai cho rắc rối.
Dùng cho: Tài khoản email, công cụ nội bộ, VPN, ứng dụng web.
Những khóa mật mã này cho phép bạn đăng nhập vào máy chủ hoặc môi trường phát triển mà không cần mật khẩu. Chúng khó bị bẻ hơn nhiều, nhưng chỉ khi được lưu trữ đúng cách.
Dùng cho: Truy cập máy chủ từ xa, quản lý hạ tầng, nền tảng đám mây.
Hãy xem chúng như thẻ ID số cho phần mềm. Chúng cấp quyền để các hệ thống giao tiếp an toàn với nhau, không cần con người can thiệp.
Dùng cho: Tích hợp, tự động hóa, pipeline CI/CD, webhook.
Vân tay, khuôn mặt, giọng nói của bạn như mật khẩu. Nhanh, tiện lợi và khó giả mạo.
Dùng cho: Đăng nhập thiết bị di động, ứng dụng công việc bảo mật, công cụ SSO.
Một ổ khóa là tốt, hai hoặc nhiều hơn thì tốt hơn. MFA thêm các lớp xác minh bổ sung, như kết hợp mật khẩu với mã tạo từ ứng dụng, quét sinh trắc học, hoặc khóa phần cứng. Ngay cả khi một yếu tố bị đánh cắp, kẻ tấn công vẫn không thể vào nếu thiếu các yếu tố còn lại.
Dùng cho: Đăng nhập an toàn vào công cụ làm việc từ xa, ứng dụng SaaS, bảng điều khiển quản trị.
Các tệp số chứng minh danh tính và mã hóa liên lạc giữa người dùng, thiết bị và trang web.
Dùng cho: HTTPS, VPN, email S/MIME, ký phần mềm.
Làm việc từ xa đã biến các lần đăng nhập của đội ngũ bạn thành chìa khóa số mở quyền truy cập vào hệ thống dữ liệu giá trị nhất và niềm tin khách hàng. Nếu không có quản lý thông tin xác thực mạnh, những chìa khóa đó có thể rơi vào tay kẻ xấu nhanh hơn bạn nghĩ.
Dưới đây là một số mối đe dọa lớn nhất đang nhắm vào thông tin xác thực an toàn trong môi trường làm việc từ xa:
Lừa đảo (Phishing): Kẻ lừa đảo dùng email, tin nhắn và trang đăng nhập giả để đánh lừa người dùng tiết lộ thông tin tài khoản.
Ghi bàn phím (Keylogging): Phần mềm độc hại âm thầm ghi lại mọi thứ được gõ, bao gồm tên người dùng, mật khẩu và token phiên.
Tấn công Brute-Force: Hacker dùng bot để đoán nhanh các cặp tên người dùng-mật khẩu, nhắm vào tài khoản dùng mật khẩu yếu hoặc tái sử dụng.
Chiếm quyền phiên (Session Hijacking): Kẻ tấn công chặn một phiên đăng nhập đang hoạt động, hành động này chiếm quyền truy cập mà không cần thông tin xác thực gốc.
Nhiều vụ vi phạm liên quan đến phiên bắt nguồn từ cài đặt RDP cấu hình sai hoặc đã lỗi thời. Tìm hiểu thêm về rủi ro và biện pháp bảo vệ bảo mật RDP để giữ môi trường từ xa của bạn an toàn.
Khi thông tin xác thực bị xâm phạm, đó không chỉ là sự bất tiện; đó là rủi ro kinh doanh. Tổ chức của bạn có thể gặp phải:
Đánh cắp dữ liệu: Tệp mật, hồ sơ tài chính hoặc thông tin khách hàng bị lộ.
Lạm dụng truy cập từ xa: Kẻ tấn công di chuyển tự do trong hệ thống khi giả làm nhân viên hợp pháp.
Gián đoạn và ngừng hoạt động: Đội IT chạy đua để khống chế sự cố trong khi công việc gần như tê liệt.
Vi phạm tuân thủ: Các khoản phạt tốn kém, chế tài và tổn hại danh tiếng lâu dài.
Tóm lại, một lần đăng nhập bị đánh cắp có thể dẫn đến phản ứng dây chuyền của các thất bại bảo mật. Đó là lý do quản lý thông tin xác thực chủ động, thay vì dọn dẹp bị động, là chiến lược thông minh hơn.
Dưới đây là các thực tiễn bảo mật truy cập từ xa quan trọng để giữ quyền truy cập thông tin xác thực của đội ngũ bạn an toàn, tinh gọn và bảo mật:
Sử dụng lưu trữ mã hóa: Lưu toàn bộ thông tin xác thực bảo mật — mật khẩu, khóa SSH, API token — trong kho mã hóa như Bitwarden hoặc 1Password. Với hệ thống rủi ro cao, dùng giải pháp phần cứng như YubiKey hoặc HSM để ngăn truy cập trái phép.
Áp dụng xác thực hai yếu tố hoặc đa yếu tố (2FA/MFA): Luôn yêu cầu ít nhất hai hình thức xác minh (ví dụ: mật khẩu + mã ứng dụng). MFA chặn hầu hết nỗ lực truy cập trái phép, ngay cả khi mật khẩu bị lộ.
Xoay vòng mật khẩu & kiểm tra quyền truy cập thường xuyên: Thiết lập chính sách hết hạn mật khẩu và xoay vòng thông tin xác thực định kỳ. Rà soát ai có quyền truy cập và loại bỏ người dùng không hoạt động để giảm rủi ro và đáp ứng yêu cầu tuân thủ.
Ngừng chia sẻ thông tin xác thực giữa các thành viên: Đăng nhập dùng chung tạo ra lỗ hổng bảo mật và vấn đề trách nhiệm. Thay vào đó, cấp tài khoản cá nhân với quyền theo vai trò. Dùng SSO hoặc nhà cung cấp danh tính để quản lý quyền dễ dàng.
Đặt thời gian chờ phiên và tự động đăng xuất: Tự động đăng xuất các phiên không hoạt động để tránh bị lạm dụng trên thiết bị không có người giám sát. Đặc biệt trong môi trường làm việc từ xa, đây là lớp bảo vệ đơn giản nhưng hiệu quả.
Muốn tìm hiểu sâu hơn về bảo mật chính máy tính từ xa của bạn? Đây là hướng dẫn đầy đủ về cách thiết lập hệ thống remote desktop an toàn đúng cách.
Một hệ thống quản lý thông tin xác thực mạnh không chỉ bảo vệ doanh nghiệp; nó còn cải thiện cách đội ngũ làm việc, cách bạn đáp ứng tuân thủ và cách bạn mở rộng an toàn trong môi trường làm việc từ xa.
Đây là những gì tổ chức của bạn có thể đạt được:
Quản lý thông tin xác thực mạnh giúp ngăn tái sử dụng mật khẩu yếu, tấn công lừa đảo và truy cập trái phép. Với các tính năng như MFA và kho mã hóa, thông tin xác thực bảo mật của bạn vẫn được bảo vệ ngay cả trên mạng và thiết bị từ xa.
Kiểm soát thông tin xác thực công ty tập trung giúp giảm công việc quản trị. Xoay vòng tự động và quyền theo vai trò rõ ràng giúp quy trình onboarding/offboarding nhanh và an toàn.
Từ GDPR đến HIPAA, kiểm soát truy cập thông tin xác thực đúng cách giúp đáp ứng các tiêu chuẩn tuân thủ toàn cầu. Nhật ký kiểm toán, mã hóa và thực thi nguyên tắc đặc quyền tối thiểu đảm bảo bạn sẵn sàng cho mọi đợt rà soát bảo mật hoặc kiểm toán bảo vệ dữ liệu mà không phát sinh quá nhiều chi phí.
Kiểm soát truy cập chi tiết giúp hạn chế người dùng được cấp quyền quá mức, trong khi giám sát phiên giúp phát hiện hoạt động đáng ngờ. Thông tin xác thực tạm thời và tính năng timeout giảm rủi ro lạm dụng thông tin xác thực về lâu dài, dù cố ý hay không.
Các công cụ như đăng nhập một lần (SSO) và kho bảo mật giúp loại bỏ ma sát đăng nhập. Người dùng xác thực một lần và truy cập thứ họ cần, không phải xoay xở với nhiều mật khẩu hoặc chịu thời gian chết. An toàn, mượt mà và hoàn hảo cho đội ngũ làm việc từ xa đang phát triển.
DeskIn là nền tảng truy cập từ xa nhanh và bảo mật, được thiết kế cho các đội ngũ hiện đại. Từ IT đến công việc sáng tạo, nó giúp người dùng kết nối và cộng tác an toàn từ bất cứ đâu.
Ngay cả mật khẩu mạnh nhất cũng không thể bảo vệ doanh nghiệp nếu nền tảng truy cập từ xa của bạn không được xây dựng cho bảo mật. Đó là lúc DeskIn phát huy, kết hợp hiệu năng với quản lý thông tin xác thực cấp doanh nghiệp để giữ mọi phiên từ xa được khóa chặt và nằm trong tầm kiểm soát của bạn.

DeskIn không cho phép bất kỳ ai vào. Nó sử dụng các phương thức đăng nhập an toàn như ghép mã thiết bị và phê duyệt phiên, đảm bảo chỉ người dùng đã xác minh mới có thể truy cập thiết bị từ xa. Dù bạn làm việc tại nhà hay ở nửa kia thế giới, DeskIn đều thực thi xác minh danh tính mạnh trước khi bất kỳ phiên nào bắt đầu.
Mọi phiên trên DeskIn đều được bảo vệ bằng mã hóa toàn phần, đảm bảo dữ liệu của bạn luôn an toàn trong quá trình truyền tải. Lớp bảo vệ đầu-cuối này giữ thông tin nhạy cảm không bị chặn bắt, ngay cả trên mạng công cộng hoặc không an toàn.
Cần truy cập hệ thống từ xa khi bạn rời bàn làm việc? DeskIn hỗ trợ truy cập không giám sát, nhưng có cơ chế bảo vệ đi kèm. Thông tin xác thực an toàn của bạn vẫn được bảo vệ bởi xác thực nhiều lớp, và quyền truy cập có thể được ghi log, giám sát để đảm bảo khả năng quan sát đầy đủ.
Với DeskIn, bạn toàn quyền kiểm soát ai được vào và từ đâu. Bằng cách dùng danh sách trắng thiết bị, bạn có thể đảm bảo chỉ thiết bị được phê duyệt trước mới kết nối vào hệ thống. Dù là một laptop hay cả đội điện thoại thông minh của công ty, bạn vẫn có kiểm soát tập trung mà không mất đi sự linh hoạt mà làm việc từ xa yêu cầu.
DeskIn không chỉ là một công cụ truy cập từ xa khác; đó là nền tảng ưu tiên bảo mật, được xây dựng với quản lý thông tin xác thực mạnh, bảo mật truy cập từ xa và giám sát thời gian thực làm cốt lõi. Từ đội thiết kế từ xa đến hỗ trợ IT đến các nhóm dev phân tán, DeskIn giúp mọi phiên được khóa chặt, mọi kết nối có thể quy trách nhiệm và mọi quy trình vận hành trơn tru.
Nếu bạn đang muốn khóa chặt hệ thống đầu-cuối, đừng bỏ lỡ hướng dẫn này về cách bảo mật remote desktop của bạn.
Bảo mật từ xa bắt đầu từ quản lý thông tin xác thực mạnh, không phải sau khi đăng nhập, mà là trước khi nó bắt đầu. Quản lý thông tin xác thực đúng cách là nền tảng của bảo mật truy cập từ xa an toàn và liền mạch.
DeskIn hỗ trợ điều này ở mọi cấp độ, từ luồng đăng nhập an toàn đến phiên mã hóa và kiểm soát truy cập cấp thiết bị. Nó giúp đội ngũ của bạn duy trì năng suất trong khi vẫn bảo vệ thông tin xác thực công ty và hệ thống.
Đây là lúc để rà soát lại thiết lập của bạn. Kiểm tra chính sách thông tin xác thực, loại bỏ điểm yếu và dùng các công cụ như DeskIn để khóa chặt phiên từ xa theo đúng cách.
Sẵn sàng kiểm soát bảo mật truy cập từ xa của bạn? Tải DeskIn ngay và bảo mật mọi lần đăng nhập.
Vẫn đang so sánh các lựa chọn? Hãy xem phân tích của chúng tôi về 10 phần mềm remote desktop bảo mật tốt nhất, và hiểu vì sao DeskIn dẫn đầu cả về bảo mật lẫn hiệu năng.

Làm việc từ xa thật tuyệt vời cho đến khi nó không còn tuyệt nữa.
Bạn có những người đang thiết kế trên Figma từ bãi biển, chốt giao dịch qua Zoom trong quán cà phê, hoặc viết code khi đang chờ ở sân bay. Nó nhanh, linh hoạt và có chút kỳ diệu. Nhưng đây là điểm mấu chốt: đằng sau mỗi cú nhấp chuột, mỗi tệp được chia sẻ, mỗi lần đăng nhập từ xa, có một thứ âm thầm giữ mọi thứ vận hành — thông tin xác thực.
Và nếu người không phù hợp nắm được những thông tin xác thực đó, mọi thứ có thể xấu đi rất nhanh.

Đó là lý do vì sao quản lý thông tin xác thực cực kỳ quan trọng, hơn bao giờ hết. Không chỉ là ghi lại mật khẩu trong một kho an toàn, mà là kiểm soát ai được truy cập vào cái gì và khi nào. Từ bảo vệ thông tin xác thực của công ty đến xoay vòng thông tin xác thực bảo mật và thiết lập MFA, đó là cách để bạn đảm bảo cánh cửa số luôn được khóa, và chỉ đúng người mới có chìa khóa.
May mắn là, các công cụ như DeskIn giúp bảo mật truy cập từ xa dễ dàng hơn rất nhiều (và thông minh hơn). Trong bài viết này, chúng tôi sẽ phân tích quản lý thông tin xác thực là gì, cách nó hoạt động, và cách bạn có thể dùng nó để khóa chặt hệ thống mà không khóa luôn cả đội ngũ của mình.
Hãy bắt đầu.
Mỗi mật khẩu, mã API, khóa SSH, chứng chỉ, hay quét vân tay về cơ bản đều là một chiếc chìa khóa cho thứ gì đó quan trọng trong thế giới số của công ty bạn. Và thành thật mà nói, theo dõi vài chiếc chìa khóa thì dễ, nhưng hàng trăm hoặc hàng nghìn chiếc thì đó là công thức cho việc mất đăng nhập, chia sẻ quá mức ngoài ý muốn, hoặc tệ hơn, vi phạm bảo mật.
Đây là lúc quản lý thông tin xác thực phát huy tác dụng. Hệ thống giữ tất cả những chìa khóa đó sẽ khóa chúng an toàn và chỉ cấp cho đúng người vào đúng thời điểm.
Một cách hình dung tốt hơn về quản lý thông tin xác thực không phải là một danh sách mật khẩu bụi bặm, mà là một “nhân viên bảo vệ” ảo biết ai nên và không nên có quyền truy cập, đảm bảo đúng người được vào và ngăn người không phù hợp ở ngoài.
Khi được triển khai đúng cách, quản lý thông tin xác thực giúp đội ngũ của bạn làm việc thông suốt đồng thời ngăn hacker và những “vị khách” không mong muốn xâm nhập.
Một thiết lập quản lý thông tin xác thực đúng chuẩn hoạt động như một đội bảo mật toàn thời gian cho các đăng nhập của bạn. Đây là những gì nó làm:
Lưu trữ an toàn – Mã hóa thông tin xác thực và giữ chúng trong kho bảo mật, tránh xa giấy nhớ dán hoặc tệp không được bảo vệ.
Truy xuất an toàn – Chỉ cung cấp thông tin xác thực cho người dùng được ủy quyền, không hiển thị dạng văn bản thuần hoặc gây rủi ro rò rỉ do sao chép-dán.
Cập nhật tự động – Xoay vòng mật khẩu, làm mới mã token và cập nhật chứng chỉ để ngăn hết hạn/bị khai thác.
Thu hồi tức thì – Cắt quyền truy cập ngay khi ai đó rời nhóm hoặc đổi vai trò, không để lại “cửa sau” nào mở.
Quản lý thông tin xác thực là nền tảng của xác thực an toàn và quản lý danh tính; thiếu nó, mọi biện pháp bảo mật khác đều trở nên yếu hơn.
Xác thực an toàn – Xác nhận danh tính từng người dùng, thêm các lớp bảo vệ như MFA, và chặn các thói quen rủi ro như tái sử dụng thông tin xác thực.
Quản lý danh tính – Gắn mỗi thông tin xác thực với một vai trò hoặc quyền cụ thể để người dùng chỉ được truy cập những gì họ thực sự cần, đồng thời giữ lại dấu vết rõ ràng, có thể kiểm toán cho mọi hành động.
Tóm lại, quản lý thông tin xác thực không chỉ bảo vệ mật khẩu; nó còn giúp bảo vệ các hoạt động số cốt lõi của doanh nghiệp bạn.

Có nhiều cấp độ thông tin xác thực là có lý do. Mỗi loại phục vụ một mục đích khác nhau, và điều quan trọng là phải hiểu cách làm việc với chúng để giữ an toàn cho làm việc từ xa. Một hệ thống quản lý thông tin xác thực mạnh không chỉ lưu trữ các thông tin này; nó biết dùng tổ hợp nào, khi nào và ở đâu. Vì vậy, dưới đây là các loại chính và lý do chúng quan trọng.
Loại thông tin xác thực kinh điển, đơn giản, quen thuộc, và không may là vẫn là mục tiêu ưa thích của kẻ tấn công. Mật khẩu yếu hoặc dùng lại là lời mời công khai cho rắc rối.
Dùng cho: Tài khoản email, công cụ nội bộ, VPN, ứng dụng web.
Những khóa mật mã này cho phép bạn đăng nhập vào máy chủ hoặc môi trường phát triển mà không cần mật khẩu. Chúng khó bị bẻ hơn nhiều, nhưng chỉ khi được lưu trữ đúng cách.
Dùng cho: Truy cập máy chủ từ xa, quản lý hạ tầng, nền tảng đám mây.
Hãy xem chúng như thẻ ID số cho phần mềm. Chúng cấp quyền để các hệ thống giao tiếp an toàn với nhau, không cần con người can thiệp.
Dùng cho: Tích hợp, tự động hóa, pipeline CI/CD, webhook.
Vân tay, khuôn mặt, giọng nói của bạn như mật khẩu. Nhanh, tiện lợi và khó giả mạo.
Dùng cho: Đăng nhập thiết bị di động, ứng dụng công việc bảo mật, công cụ SSO.
Một ổ khóa là tốt, hai hoặc nhiều hơn thì tốt hơn. MFA thêm các lớp xác minh bổ sung, như kết hợp mật khẩu với mã tạo từ ứng dụng, quét sinh trắc học, hoặc khóa phần cứng. Ngay cả khi một yếu tố bị đánh cắp, kẻ tấn công vẫn không thể vào nếu thiếu các yếu tố còn lại.
Dùng cho: Đăng nhập an toàn vào công cụ làm việc từ xa, ứng dụng SaaS, bảng điều khiển quản trị.
Các tệp số chứng minh danh tính và mã hóa liên lạc giữa người dùng, thiết bị và trang web.
Dùng cho: HTTPS, VPN, email S/MIME, ký phần mềm.
Làm việc từ xa đã biến các lần đăng nhập của đội ngũ bạn thành chìa khóa số mở quyền truy cập vào hệ thống dữ liệu giá trị nhất và niềm tin khách hàng. Nếu không có quản lý thông tin xác thực mạnh, những chìa khóa đó có thể rơi vào tay kẻ xấu nhanh hơn bạn nghĩ.
Dưới đây là một số mối đe dọa lớn nhất đang nhắm vào thông tin xác thực an toàn trong môi trường làm việc từ xa:
Lừa đảo (Phishing): Kẻ lừa đảo dùng email, tin nhắn và trang đăng nhập giả để đánh lừa người dùng tiết lộ thông tin tài khoản.
Ghi bàn phím (Keylogging): Phần mềm độc hại âm thầm ghi lại mọi thứ được gõ, bao gồm tên người dùng, mật khẩu và token phiên.
Tấn công Brute-Force: Hacker dùng bot để đoán nhanh các cặp tên người dùng-mật khẩu, nhắm vào tài khoản dùng mật khẩu yếu hoặc tái sử dụng.
Chiếm quyền phiên (Session Hijacking): Kẻ tấn công chặn một phiên đăng nhập đang hoạt động, hành động này chiếm quyền truy cập mà không cần thông tin xác thực gốc.
Nhiều vụ vi phạm liên quan đến phiên bắt nguồn từ cài đặt RDP cấu hình sai hoặc đã lỗi thời. Tìm hiểu thêm về rủi ro và biện pháp bảo vệ bảo mật RDP để giữ môi trường từ xa của bạn an toàn.
Khi thông tin xác thực bị xâm phạm, đó không chỉ là sự bất tiện; đó là rủi ro kinh doanh. Tổ chức của bạn có thể gặp phải:
Đánh cắp dữ liệu: Tệp mật, hồ sơ tài chính hoặc thông tin khách hàng bị lộ.
Lạm dụng truy cập từ xa: Kẻ tấn công di chuyển tự do trong hệ thống khi giả làm nhân viên hợp pháp.
Gián đoạn và ngừng hoạt động: Đội IT chạy đua để khống chế sự cố trong khi công việc gần như tê liệt.
Vi phạm tuân thủ: Các khoản phạt tốn kém, chế tài và tổn hại danh tiếng lâu dài.
Tóm lại, một lần đăng nhập bị đánh cắp có thể dẫn đến phản ứng dây chuyền của các thất bại bảo mật. Đó là lý do quản lý thông tin xác thực chủ động, thay vì dọn dẹp bị động, là chiến lược thông minh hơn.
Dưới đây là các thực tiễn bảo mật truy cập từ xa quan trọng để giữ quyền truy cập thông tin xác thực của đội ngũ bạn an toàn, tinh gọn và bảo mật:
Sử dụng lưu trữ mã hóa: Lưu toàn bộ thông tin xác thực bảo mật — mật khẩu, khóa SSH, API token — trong kho mã hóa như Bitwarden hoặc 1Password. Với hệ thống rủi ro cao, dùng giải pháp phần cứng như YubiKey hoặc HSM để ngăn truy cập trái phép.
Áp dụng xác thực hai yếu tố hoặc đa yếu tố (2FA/MFA): Luôn yêu cầu ít nhất hai hình thức xác minh (ví dụ: mật khẩu + mã ứng dụng). MFA chặn hầu hết nỗ lực truy cập trái phép, ngay cả khi mật khẩu bị lộ.
Xoay vòng mật khẩu & kiểm tra quyền truy cập thường xuyên: Thiết lập chính sách hết hạn mật khẩu và xoay vòng thông tin xác thực định kỳ. Rà soát ai có quyền truy cập và loại bỏ người dùng không hoạt động để giảm rủi ro và đáp ứng yêu cầu tuân thủ.
Ngừng chia sẻ thông tin xác thực giữa các thành viên: Đăng nhập dùng chung tạo ra lỗ hổng bảo mật và vấn đề trách nhiệm. Thay vào đó, cấp tài khoản cá nhân với quyền theo vai trò. Dùng SSO hoặc nhà cung cấp danh tính để quản lý quyền dễ dàng.
Đặt thời gian chờ phiên và tự động đăng xuất: Tự động đăng xuất các phiên không hoạt động để tránh bị lạm dụng trên thiết bị không có người giám sát. Đặc biệt trong môi trường làm việc từ xa, đây là lớp bảo vệ đơn giản nhưng hiệu quả.
Muốn tìm hiểu sâu hơn về bảo mật chính máy tính từ xa của bạn? Đây là hướng dẫn đầy đủ về cách thiết lập hệ thống remote desktop an toàn đúng cách.
Một hệ thống quản lý thông tin xác thực mạnh không chỉ bảo vệ doanh nghiệp; nó còn cải thiện cách đội ngũ làm việc, cách bạn đáp ứng tuân thủ và cách bạn mở rộng an toàn trong môi trường làm việc từ xa.
Đây là những gì tổ chức của bạn có thể đạt được:
Quản lý thông tin xác thực mạnh giúp ngăn tái sử dụng mật khẩu yếu, tấn công lừa đảo và truy cập trái phép. Với các tính năng như MFA và kho mã hóa, thông tin xác thực bảo mật của bạn vẫn được bảo vệ ngay cả trên mạng và thiết bị từ xa.
Kiểm soát thông tin xác thực công ty tập trung giúp giảm công việc quản trị. Xoay vòng tự động và quyền theo vai trò rõ ràng giúp quy trình onboarding/offboarding nhanh và an toàn.
Từ GDPR đến HIPAA, kiểm soát truy cập thông tin xác thực đúng cách giúp đáp ứng các tiêu chuẩn tuân thủ toàn cầu. Nhật ký kiểm toán, mã hóa và thực thi nguyên tắc đặc quyền tối thiểu đảm bảo bạn sẵn sàng cho mọi đợt rà soát bảo mật hoặc kiểm toán bảo vệ dữ liệu mà không phát sinh quá nhiều chi phí.
Kiểm soát truy cập chi tiết giúp hạn chế người dùng được cấp quyền quá mức, trong khi giám sát phiên giúp phát hiện hoạt động đáng ngờ. Thông tin xác thực tạm thời và tính năng timeout giảm rủi ro lạm dụng thông tin xác thực về lâu dài, dù cố ý hay không.
Các công cụ như đăng nhập một lần (SSO) và kho bảo mật giúp loại bỏ ma sát đăng nhập. Người dùng xác thực một lần và truy cập thứ họ cần, không phải xoay xở với nhiều mật khẩu hoặc chịu thời gian chết. An toàn, mượt mà và hoàn hảo cho đội ngũ làm việc từ xa đang phát triển.
DeskIn là nền tảng truy cập từ xa nhanh và bảo mật, được thiết kế cho các đội ngũ hiện đại. Từ IT đến công việc sáng tạo, nó giúp người dùng kết nối và cộng tác an toàn từ bất cứ đâu.
Ngay cả mật khẩu mạnh nhất cũng không thể bảo vệ doanh nghiệp nếu nền tảng truy cập từ xa của bạn không được xây dựng cho bảo mật. Đó là lúc DeskIn phát huy, kết hợp hiệu năng với quản lý thông tin xác thực cấp doanh nghiệp để giữ mọi phiên từ xa được khóa chặt và nằm trong tầm kiểm soát của bạn.

DeskIn không cho phép bất kỳ ai vào. Nó sử dụng các phương thức đăng nhập an toàn như ghép mã thiết bị và phê duyệt phiên, đảm bảo chỉ người dùng đã xác minh mới có thể truy cập thiết bị từ xa. Dù bạn làm việc tại nhà hay ở nửa kia thế giới, DeskIn đều thực thi xác minh danh tính mạnh trước khi bất kỳ phiên nào bắt đầu.
Mọi phiên trên DeskIn đều được bảo vệ bằng mã hóa toàn phần, đảm bảo dữ liệu của bạn luôn an toàn trong quá trình truyền tải. Lớp bảo vệ đầu-cuối này giữ thông tin nhạy cảm không bị chặn bắt, ngay cả trên mạng công cộng hoặc không an toàn.
Cần truy cập hệ thống từ xa khi bạn rời bàn làm việc? DeskIn hỗ trợ truy cập không giám sát, nhưng có cơ chế bảo vệ đi kèm. Thông tin xác thực an toàn của bạn vẫn được bảo vệ bởi xác thực nhiều lớp, và quyền truy cập có thể được ghi log, giám sát để đảm bảo khả năng quan sát đầy đủ.
Với DeskIn, bạn toàn quyền kiểm soát ai được vào và từ đâu. Bằng cách dùng danh sách trắng thiết bị, bạn có thể đảm bảo chỉ thiết bị được phê duyệt trước mới kết nối vào hệ thống. Dù là một laptop hay cả đội điện thoại thông minh của công ty, bạn vẫn có kiểm soát tập trung mà không mất đi sự linh hoạt mà làm việc từ xa yêu cầu.
DeskIn không chỉ là một công cụ truy cập từ xa khác; đó là nền tảng ưu tiên bảo mật, được xây dựng với quản lý thông tin xác thực mạnh, bảo mật truy cập từ xa và giám sát thời gian thực làm cốt lõi. Từ đội thiết kế từ xa đến hỗ trợ IT đến các nhóm dev phân tán, DeskIn giúp mọi phiên được khóa chặt, mọi kết nối có thể quy trách nhiệm và mọi quy trình vận hành trơn tru.
Nếu bạn đang muốn khóa chặt hệ thống đầu-cuối, đừng bỏ lỡ hướng dẫn này về cách bảo mật remote desktop của bạn.
Bảo mật từ xa bắt đầu từ quản lý thông tin xác thực mạnh, không phải sau khi đăng nhập, mà là trước khi nó bắt đầu. Quản lý thông tin xác thực đúng cách là nền tảng của bảo mật truy cập từ xa an toàn và liền mạch.
DeskIn hỗ trợ điều này ở mọi cấp độ, từ luồng đăng nhập an toàn đến phiên mã hóa và kiểm soát truy cập cấp thiết bị. Nó giúp đội ngũ của bạn duy trì năng suất trong khi vẫn bảo vệ thông tin xác thực công ty và hệ thống.
Đây là lúc để rà soát lại thiết lập của bạn. Kiểm tra chính sách thông tin xác thực, loại bỏ điểm yếu và dùng các công cụ như DeskIn để khóa chặt phiên từ xa theo đúng cách.
Sẵn sàng kiểm soát bảo mật truy cập từ xa của bạn? Tải DeskIn ngay và bảo mật mọi lần đăng nhập.
Vẫn đang so sánh các lựa chọn? Hãy xem phân tích của chúng tôi về 10 phần mềm remote desktop bảo mật tốt nhất, và hiểu vì sao DeskIn dẫn đầu cả về bảo mật lẫn hiệu năng.


DeskIn vs Chrome Remote Desktop: Which One Fits Your Workflow Best?
When it comes to remote access tools, the comparison between DeskIn and Chrome Remote Desktop often comes down to one simple question: do you just need quick access, or do you need performance and control?
Both tools are reliable, secure, and widely used. But they are built for very different types of users. Chrome Remote Desktop focuses on simplicity and accessibility, while DeskIn is designed for users who need high performance, stability, and advanced features across multiple devices.
If you're deciding between the two, this guide breaks down not just what they offer, but which one actually fits your workflow.
Feature | DeskIn | Chrome Remote Desktop |
|---|---|---|
Performance | Up to 4K 60FPS/2K 240FPS, low latency | Standard performance |
Ease of Use | Requires app installation | Browser-based, very simple |
Device Support | Windows, macOS, iOS, Android | Works via Chrome browser |
File Transfer | Fast and stable | Limited |
Multi-device Management | Yes | No |
Mobile Experience | Optimized for iPad & iPhone | Basic |
Security | Privacy screens and granular black/whitelists | Basic |
Price | Free + paid plans | Completely free |
In short, Chrome Remote Desktop is great for quick, lightweight access, while DeskIn is built for users who expect more from their remote desktop experience.

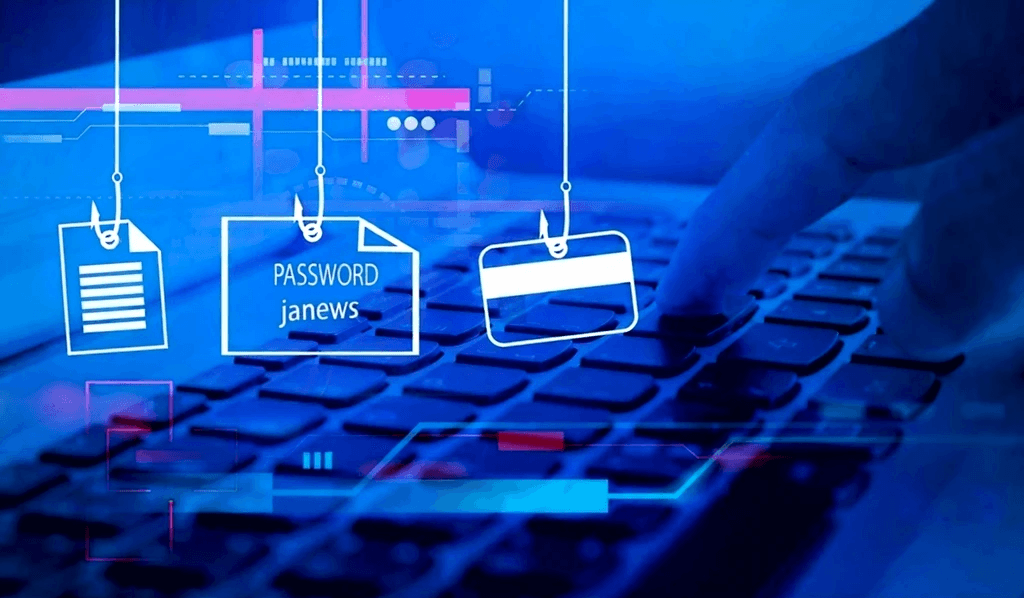
Chrome Remote Desktop is one of the simplest remote access tools available. It runs directly through the Chrome browser and requires only a Google account to get started. This makes it especially popular among casual users and those already working within the Google ecosystem.
It works particularly well on devices like Chromebooks, where everything is already browser-based. It's also accessible across platforms, including mobile devices like iPhone and iPad, though the experience on mobile can feel limited compared to desktop use.
If you're wondering how to use Chrome Remote Desktop, the process is straightforward. You install the Chrome extension, sign in with your Google account, set up a PIN on the host device, and then connect from another device using the same account. The entire setup usually takes just a few minutes.
That said, simplicity comes with trade-offs. Chrome Remote Desktop lacks advanced features like high frame rate streaming, multi-monitor control, or professional-grade file transfer. For occasional access, it works well. But for more demanding tasks, users often start to feel its limitations.
👀You may also be interested in:
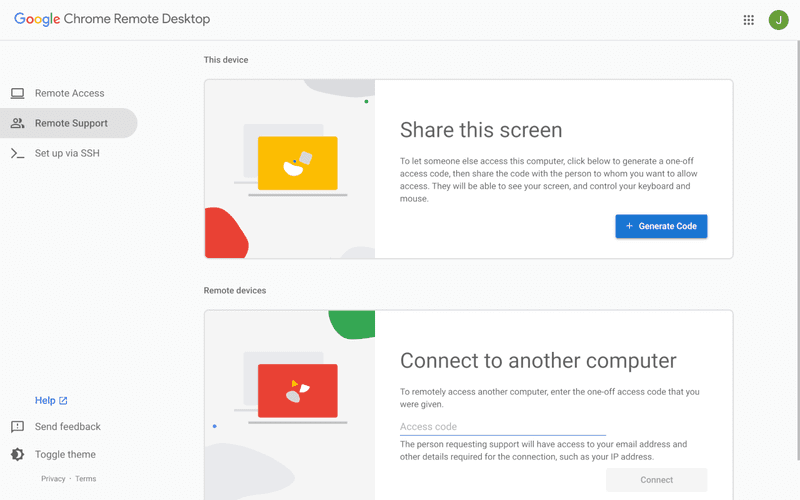
If Chrome Remote Desktop is a lightweight sketch, DeskIn is a full workstation painted in high resolution. DeskIn focuses on performance, stability, and flexibility. It supports up to 4K 60FPS streaming, making it suitable for tasks where visual clarity and responsiveness matter, such as design work, video editing, or even gaming.
As a Chrome remote desktop alternative, unlike browser-based tools, DeskIn is a dedicated remote desktop application. While this requires installation, it unlocks a much more stable and feature-rich experience. Users can manage multiple devices, transfer large files efficiently, and enjoy smoother control across different platforms.
DeskIn is also optimized for mobile workflows. Whether you're using an iPad or smartphone, the interaction feels more responsive and closer to a desktop experience, rather than a simplified viewer. For users who find Chrome Remote Desktop "good enough" at first but limiting over time, DeskIn often becomes the natural upgrade path.
The real difference between these two tools becomes clear when you look at how they perform in everyday scenarios.
If you only need to check files on your home computer or help a friend troubleshoot something quickly, Chrome Remote Desktop is more than enough. It's free, easy to set up, and doesn't require installing extra software beyond Chrome. In this case, DeskIn may feel like overkill.
For professionals working remotely on a daily basis, stability and efficiency matter much more. This is where DeskIn starts to stand out.
Tasks like editing documents, managing multiple screens, or transferring files between devices become smoother and faster. Chrome Remote Desktop can handle basic workflows, but it often struggles with responsiveness and lacks the tools needed for a seamless work environment.
This is where the gap becomes impossible to ignore. DeskIn's support for high resolution and high frame rates makes it suitable for visually demanding work. Whether you're editing videos, working with design software, or running simulations, performance consistency is critical. Chrome Remote Desktop, on the other hand, is not designed for these scenarios. It works, but not comfortably.
If you rely heavily on Google services or use a Chromebook, Chrome Remote Desktop integrates naturally into your workflow. It's lightweight, requires no additional setup, and feels like an extension of the browser itself. In this scenario, it remains a very practical choice.
Mobile usage highlights another important difference. While remote desktop Chrome iPhone, and Chrome Remote Desktop iPad are functional, they often feel like simplified versions of the desktop experience. Controls can be less intuitive, and performance may vary depending on the connection.
DeskIn, by contrast, is designed with cross-device interaction in mind, offering a smoother and more responsive mobile experience.
👀 You may also be interested in:
Yes. Tools like DeskIn offer better performance, more features, and improved stability, especially for professional use cases.
No, Chrome Remote Desktop is still actively maintained by Google. It continues to receive security updates and remains available for users needing simple, free remote access.
Yes, DeskIn is a legitimate remote desktop solution. It uses encryption to secure connections and provides access controls, making it safe for both personal and professional use.
When comparing DeskIn vs Chrome Remote Desktop, the choice depends on how demanding your remote access needs are. Chrome Remote Desktop is simple, free, and ideal for occasional use, especially if you just need quick access to a device without extra setup.
As your workflow becomes more intensive, the limitations start to surface. DeskIn offers a smoother, more stable experience with better performance and control, making it a strong long-term Chrome remote desktop alternative for users who rely on remote access every day.


8 Best Remote Desktops for Video Editing in 2026
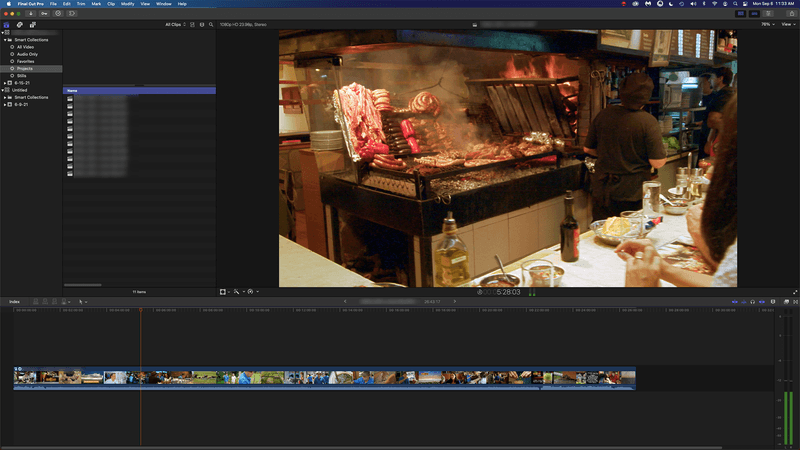
Remote video editing is no longer a compromise; it's a workflow upgrade. Whether you're working in Adobe Premiere Pro, After Effects, or DaVinci Resolve, the right remote desktop can turn your laptop into a high-performance editing station.
But not all tools are built for remote video editing collaboration. Lag, poor color accuracy, and unstable connections can ruin productivity. In this guide, we'll break down the best remote desktop for video editing tools so that you can edit smoothly from anywhere.
Modern creators are no longer tied to a single workstation. With remote work software, you can access your powerful desktop from anywhere without investing in an expensive laptop. For many editors, especially freelancers and small teams, this solves a real problem: you already have a high-performance PC, but mobility is limited. Instead of duplicating hardware, video editing remote desktop tools let you stream your workflow in real time.
Another key benefit is remote collaboration. Teams can work on the same project across different locations, review edits instantly, and avoid large file transfers via remote collaboration tools. However, this only works if your remote desktop software supports high frame rates, low latency, and stable connections. Otherwise, editing becomes frustrating.

Here's a quick overview of the best tools and who they're for:
DeskIn – Best overall for performance + affordability + multi-device workflows
Parsec – Best for ultra-low latency editing
Splashtop – Best for high-resolution streaming
HP Anyware – Best for enterprise-level workflows
Jump Desktop – Best for Mac users
AnyDesk – Best lightweight remote access
Chrome Remote Desktop – Best free basic option
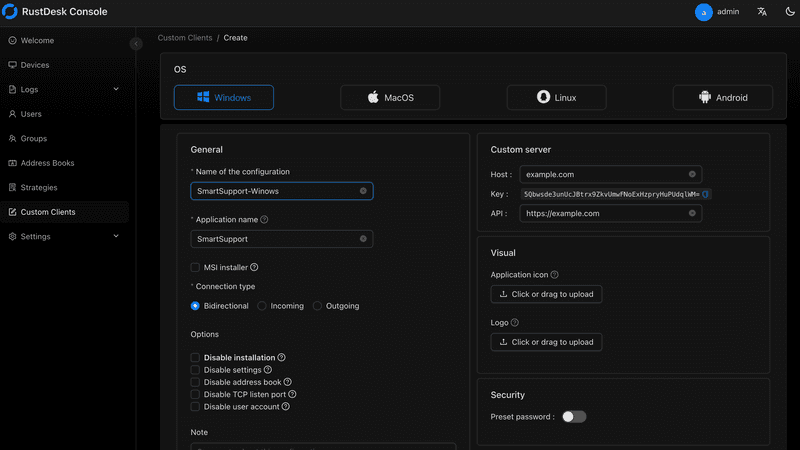
RustDesk – Best open-source alternative
Up to 4K 60FPS / 2K 240FPS performance
Ultra-low latency for smooth editing timelines
Multi-device support (PC, Mac, iPad, Android)
Affordable pricing with free plan available
Smaller brand awareness compared to legacy tools

DeskIn stands out as the best remote desktop for video editing by balancing performance, stability, and accessibility. Unlike many traditional remote support tools, it is designed for high-frame-rate tasks, making timeline scrubbing, preview playback, and effects editing feel responsive and fluid.
For creators working across devices, DeskIn enables seamless remote video editing collaboration. You can access your main editing PC from a laptop, tablet, or even a secondary workstation without noticeable lag. Compared to tools like Chrome Remote Desktop, which struggle with video-heavy workloads, DeskIn maintains consistent quality and responsiveness—making it a practical choice for both solo editors and distributed teams.

Extremely low latency
High frame rate streaming
Popular among creative professionals
Limited collaboration features
Setup can be complex for beginners
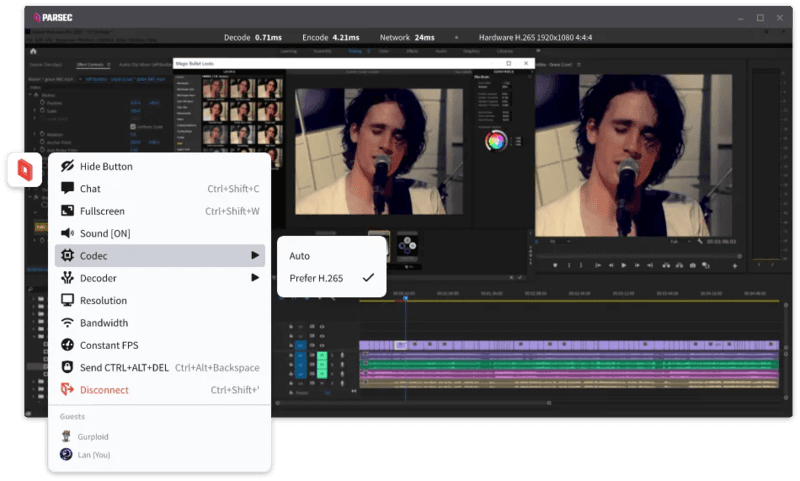
Parsec is widely recognized as a top choice for remote video editing, especially when latency is your biggest concern. Its streaming technology is optimized for real-time responsiveness, which makes it ideal for tasks like timeline scrubbing and motion graphics work in After Effects.
However, while Parsec excels in performance, it lacks some features needed for full remote video editing collaboration. Multi-user workflows and advanced access control are not as robust as some newer tools. For users who need both performance and flexibility, alternatives like DeskIn may provide a more balanced solution.
Supports 4K streaming
Strong color accuracy
Reliable for creative tasks
Higher cost for advanced features
Can experience latency over long distances

Splashtop is a solid option for editors who prioritize visual fidelity. Its support for high-resolution streaming and 4:4:4 color makes it suitable for color grading and detailed editing work.
That said, performance consistency can vary depending on network conditions. Some users report lag when working outside local networks. Compared to more optimized remote work software like DeskIn, Splashtop may require a stronger connection to maintain the same level of smoothness.
Industry-grade performance
Secure and scalable
Used in professional studios
Expensive
Complex setup
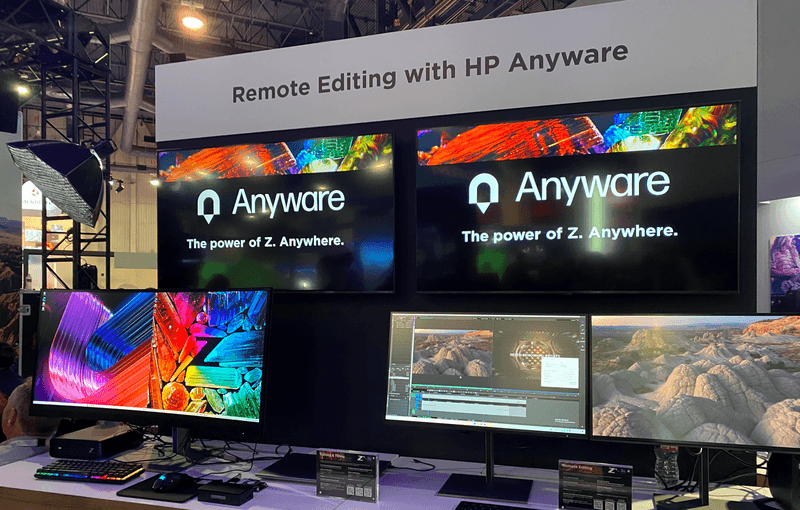
HP Anyware (formerly Teradici) is designed for high-end production environments. It uses advanced protocols to deliver excellent performance and security, making it a common choice in the media and entertainment industries.
However, for small teams or individual creators, it may be overkill. The cost and setup complexity make it less accessible compared to modern remote desktops for video editing tools that offer similar performance with easier deployment. The high cost and technical complexity create barriers that modern remote desktop solutions have eliminated, like DeskIn, offering comparable performance with far simpler deployment.
Great macOS integration
Smooth performance
Easy to use
Limited advanced features
Not ideal for heavy collaboration
Jump Desktop has earned a loyal following among Mac users seeking a straightforward, efficient remote desktop for video editing. Its Fluid Remote Desktop protocol provides smooth, responsive performance for most editing tasks without unnecessary complexity.
Where it falls short is in collaboration. Jump Desktop is built for individual use, lacking the team-oriented features that creative groups need. For solo professionals, it works well, but teams will quickly miss real-time collaboration tools found on other platforms.
Pros
Fast and lightweight
Easy to set up
Works on multiple devices
Cons
Limited performance for video editing
Lower visual quality
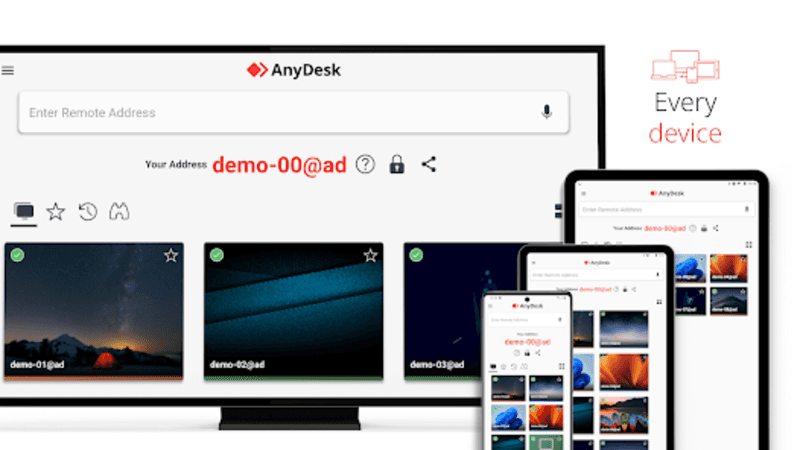
AnyDesk has built its reputation on lightweight design and remarkable ease of use for general remote access. It handles everyday tasks competently, connecting quickly and running smoothly on modest hardware.
The limitations become apparent with demanding creative work. Remote video editing requires consistent frame rates and crystal-clear visuals—areas where AnyDesk struggles. For professional editors who need precision, the performance gap becomes impossible to ignore.
Completely free
Easy browser-based setup
Works on any device
Poor performance for editing
Limited features
Chrome Remote Desktop is one of the most accessible remote support tools, offering a simple way to access your computer from anywhere. It's free, requires almost no setup, and lets you access your computer from anywhere with just a browser. For basic technical support or quick file grabs, it gets the job done.
However, it is not built for remote video editing. Users often experience lag, compression artifacts, and low frame rates. If you're working on professional projects, upgrading to a more capable solution is highly recommended.
Open-source
Self-hosting available
Free to use
Requires technical setup
Performance can vary
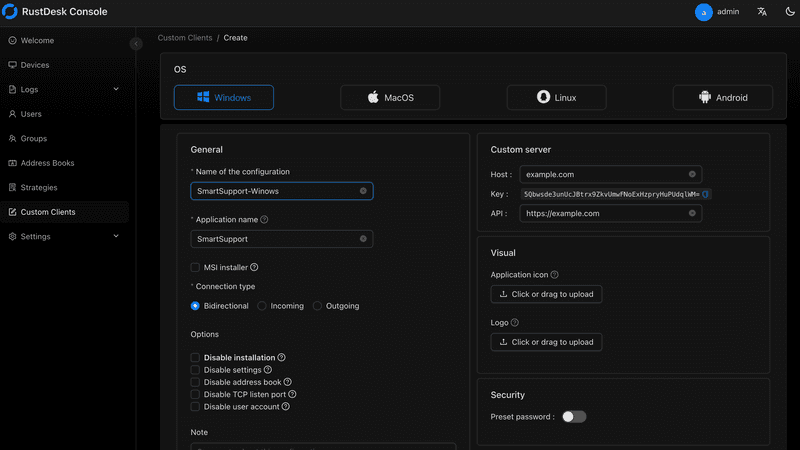
RustDesk appeals to users who prioritize open-source philosophy and want complete control over their remote access infrastructure. The flexibility to self-host and customize is genuinely valuable for privacy-conscious users. RustDesk is an interesting option for users who prefer open-source remote desktop not working alternatives or want full control over their infrastructure.
Performance, however, depends entirely on your configuration skills. Without technical expertise, achieving the smooth, low-latency experience required for professional editing is challenging. It's powerful for those who know how to tune it, but not plug-and-play.
Yes, with the right remote desktop for video editing, you can edit videos smoothly from anywhere. Tools like DeskIn and Parsec provide low latency and high frame rates for professional workflows.
Free options like Chrome Remote Desktop exist, but they lack performance. DeskIn offers a free plan with better performance, making it a stronger choice for real editing work.
Yes, Parsec is excellent for low-latency editing. However, it may lack collaboration features needed for team workflows.
Common issues include poor network connection, low bandwidth, or software limitations. Choosing optimized remote work software like DeskIn can significantly improve performance.
Choosing the best remote desktop for video editing depends on your workflow, budget, and performance needs. While tools like Parsec and Splashtop excel in specific areas, many solutions struggle to balance performance, stability, and usability.
If you're looking for a well-rounded solution, DeskIn offers a strong combination of high performance, smooth streaming, and cross-device flexibility. Whether you're working solo or collaborating remotely, it provides a reliable foundation for modern remote video editing workflows.


Unlocking the Ultimate Remote Work Setup: Deskimo Meets DeskIn
Remote work promised freedom, but for many professionals it quietly delivered a new kind of friction. The apartment is too noisy. The café Wi-Fi is patchy. The laptop bag gets heavier every month as cables, chargers, and a second monitor piles on. Somewhere along the way, "working from anywhere" started to feel a lot like hauling your office everywhere.
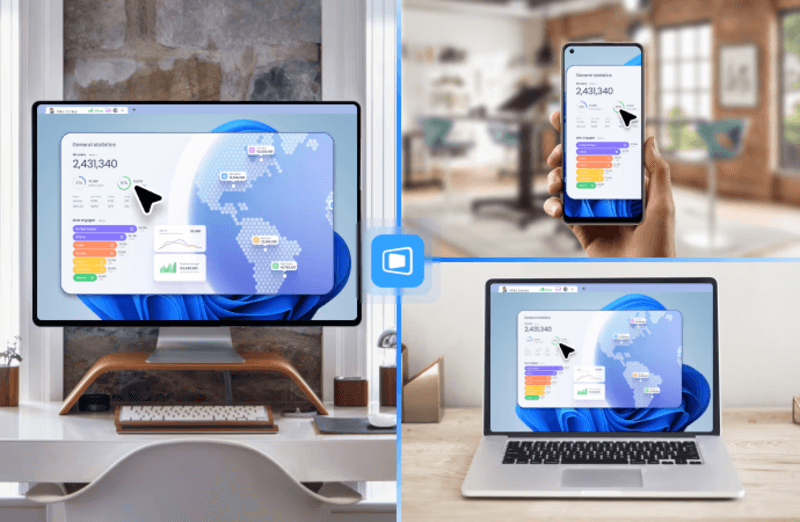
The fix is to pair two tools that solve opposite halves of the same problem. Deskimo, a coworking space platform, gives you on-demand access to workspaces by the minute. DeskIn, a remote desktop software, gives you access to your home or office computer from any device. Put them together and you get a workflow that removes hardware limits, keeps your data on your home machine, and lets you walk into any city with nothing but a tablet.
Working from home sounds ideal until your partner takes a call in the shared study. Or when the neighbour upstairs starts drilling at 9 a.m. Most work requires deep engagement and intense focus, free from distractions. Most homes were not designed to provide these on demand.
Coworking spaces fill this gap in three ways. Firstly, they set a physical boundary between personal life and work. Research suggests coworking setup is linked to higher productivity than working from home. Secondly, they offer amenities that are difficult to replicate at home: strong Wi-Fi, ergonomic chairs, private meeting rooms and quiet zones. Thirdly, individual workstations, open-plan workspaces foster a professional presence. You are most likely surrounded by people who are also there to work, and this social context encourages you to do the same.
The downside of most coworking spaces is the commitment. Monthly memberships and yearly office leases assume you need a desk every day, but most remote workers don't. Deskimo removes that friction: book a desk or meeting room by the hour, only when you need it, at hundreds of locations across cities.

Once you start working outside of home regularly, the first thing you'll notice is the bag. A full laptop setup - machine, charger, mouse, maybe a portable monitor - adds up fast, especially if you're commuting by train or bike.
The fix is simple: leave your powerful machine at home. Carry only a lightweight tablet or thin laptop. DeskIn bridges the gap: open the app on your tablet, connect to your home workstation, and your full desktop environment streams to your screen. CAD software, video editing timelines, 40-tab research sessions. Everything runs on your hardware at home while you sit at a Deskimo desk across town.
A typical morning might start with email and focused work at a café-style hot desk over coffee. After lunch, you book a Deskimo private meeting room, connect to your home workstation through DeskIn, and tackle the heavy rendering or design work. Your bag weighs less than a paperback. Your output doesn't change.
Working on public Wi-Fi has always been a quiet risk. When you open sensitive files on a portable device at a hot desk, those files are now physically travelling with you on a drive that could be stolen or compromised.
DeskIn's architecture sidesteps this. Your work runs on your home or office machine; the actual files never leave your network. Your device becomes a window: it displays pixels, sends back your clicks and keystrokes, and stores nothing from the session. Combined with DeskIn's end-to-end encryption and Privacy Mode (which blanks the host screen so no passerby sees what you're working on), the setup is arguably safer than carrying a laptop.
This matters most for teams working with regulated data - legal, healthcare, finance. Now you can offer staff the freedom to work from any Deskimo location without stretching your security perimeter to every space they visit.

One of the underrated benefits of coworking spaces is that they often provide equipment that you wouldn't buy. Many Deskimo locations have meeting rooms equipped with external monitors, smart TVs or dual-display desks. Check the amenities at your chosen location and ask the staff if this is important for your session.
DeskIn's screen management feature allows you to make the most of these setups without the need for additional cables or adapters. You can wirelessly extend your remote desktop across multiple displays, which is a great upgrade for anyone working with spreadsheets, design files or code. For example, you could put financial models on one screen, reference documents on another, communication on a third; all without buying a single monitor.
The idea is appealing, but the practical question is where to begin. Here are a few guidelines:
If focusing at home has been a struggle, book a few Deskimo sessions across different locations and see what clicks. Some people thrive in café energy; others need a silent private booth. Once you know where you work best, install DeskIn on both your desktop and your portable device. Spend a session fine-tuning the connection before you depend on it for work.
Open coworking areas suit light communication and email. Quiet zones are better for focused writing or deep analysis. Private meeting rooms belong to client calls and heavy multi-screen work. With Deskimo's pay-per-minute pricing, you only pay for the room type you actually need; no overspending on a meeting room when a hot desk will do.
A permanent private office in a major city can run from several hundred to several thousand dollars a month. A combined Deskimo and DeskIn setup, used a few days a week, typically costs at a fraction of that, before you even count the hardware you no longer need to buy. Ask the Deskimo staff about location pricing and team plans, as costs vary by city and space type.
Coworking spaces are not a perfect substitute for a dedicated office. Availability fluctuates, noise levels vary, and long sessions on pay-per-minute pricing is costly. The fix is simple: book ahead for important sessions, have an alternative location in mind, and use Deskimo day passes or bundles when you know you'll be there all day.
If you are using remote desktop software to work but struggle with noisy home environments, a coworking space could be the missing piece. Try booking a workspace on Deskimo app using the referral code DESKIN to get for $10 off (new users only). Setting up a new Deskimo Business account? Use referral code DESKBIZ for 60% off your first credit package. If you already have a Deskimo membership but find yourself hauling heavy gears to every session, DeskIn could change that. Download the app, connect to your desktop in minutes. Use promo code DESKIMO for 50% off DeskIn for the first month (or 20% off on annual plans). This promotion is valid until 31 July 2026. Terms and conditions apply.
The best remote setup isn't about buying more gear. It's about showing up anywhere with almost nothing, and still doing your best work.

Deskimo is an on-demand workspace platform that gives professionals pay-per-minute access to coworking spaces, private offices, and meeting rooms. No long-term leases. No monthly subscriptions. Book a space when you need it and only pay for the time you use.
DeskIn is remote desktop software that delivers low-latency access to your personal and enterprise computers from any device. With end-to-end encryption, multi-screen management, and fast data transmission, it's made for professionals who need all the power of a desktop computer without having to carry the hardware.

DeskIn vs Chrome Remote Desktop: Which One Fits Your Workflow Best?
When it comes to remote access tools, the comparison between DeskIn and Chrome Remote Desktop often comes down to one simple question: do you just need quick access, or do you need performance and control?
Both tools are reliable, secure, and widely used. But they are built for very different types of users. Chrome Remote Desktop focuses on simplicity and accessibility, while DeskIn is designed for users who need high performance, stability, and advanced features across multiple devices.
If you're deciding between the two, this guide breaks down not just what they offer, but which one actually fits your workflow.
Feature | DeskIn | Chrome Remote Desktop |
|---|---|---|
Performance | Up to 4K 60FPS/2K 240FPS, low latency | Standard performance |
Ease of Use | Requires app installation | Browser-based, very simple |
Device Support | Windows, macOS, iOS, Android | Works via Chrome browser |
File Transfer | Fast and stable | Limited |
Multi-device Management | Yes | No |
Mobile Experience | Optimized for iPad & iPhone | Basic |
Security | Privacy screens and granular black/whitelists | Basic |
Price | Free + paid plans | Completely free |
In short, Chrome Remote Desktop is great for quick, lightweight access, while DeskIn is built for users who expect more from their remote desktop experience.

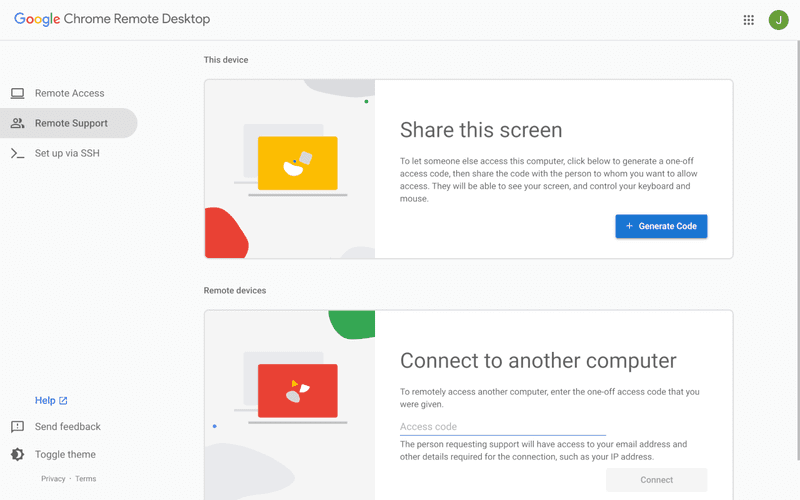
Chrome Remote Desktop is one of the simplest remote access tools available. It runs directly through the Chrome browser and requires only a Google account to get started. This makes it especially popular among casual users and those already working within the Google ecosystem.
It works particularly well on devices like Chromebooks, where everything is already browser-based. It's also accessible across platforms, including mobile devices like iPhone and iPad, though the experience on mobile can feel limited compared to desktop use.
If you're wondering how to use Chrome Remote Desktop, the process is straightforward. You install the Chrome extension, sign in with your Google account, set up a PIN on the host device, and then connect from another device using the same account. The entire setup usually takes just a few minutes.
That said, simplicity comes with trade-offs. Chrome Remote Desktop lacks advanced features like high frame rate streaming, multi-monitor control, or professional-grade file transfer. For occasional access, it works well. But for more demanding tasks, users often start to feel its limitations.
👀You may also be interested in:
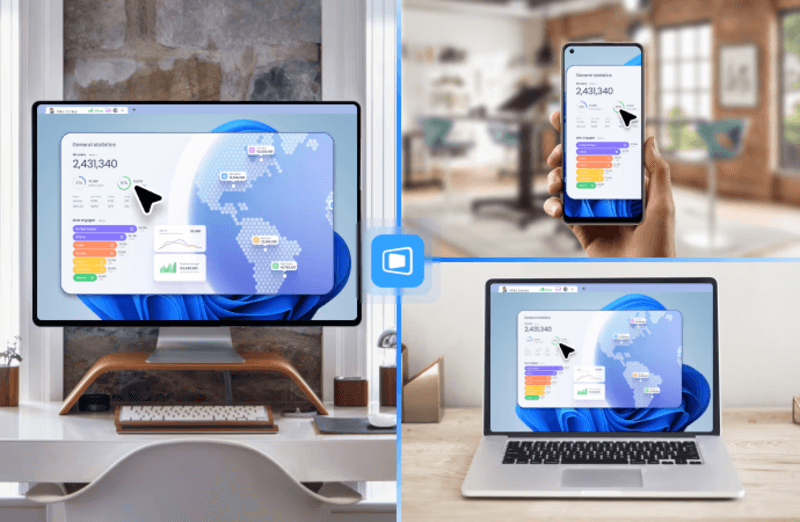
If Chrome Remote Desktop is a lightweight sketch, DeskIn is a full workstation painted in high resolution. DeskIn focuses on performance, stability, and flexibility. It supports up to 4K 60FPS streaming, making it suitable for tasks where visual clarity and responsiveness matter, such as design work, video editing, or even gaming.
As a Chrome remote desktop alternative, unlike browser-based tools, DeskIn is a dedicated remote desktop application. While this requires installation, it unlocks a much more stable and feature-rich experience. Users can manage multiple devices, transfer large files efficiently, and enjoy smoother control across different platforms.
DeskIn is also optimized for mobile workflows. Whether you're using an iPad or smartphone, the interaction feels more responsive and closer to a desktop experience, rather than a simplified viewer. For users who find Chrome Remote Desktop "good enough" at first but limiting over time, DeskIn often becomes the natural upgrade path.
The real difference between these two tools becomes clear when you look at how they perform in everyday scenarios.
If you only need to check files on your home computer or help a friend troubleshoot something quickly, Chrome Remote Desktop is more than enough. It's free, easy to set up, and doesn't require installing extra software beyond Chrome. In this case, DeskIn may feel like overkill.
For professionals working remotely on a daily basis, stability and efficiency matter much more. This is where DeskIn starts to stand out.
Tasks like editing documents, managing multiple screens, or transferring files between devices become smoother and faster. Chrome Remote Desktop can handle basic workflows, but it often struggles with responsiveness and lacks the tools needed for a seamless work environment.
This is where the gap becomes impossible to ignore. DeskIn's support for high resolution and high frame rates makes it suitable for visually demanding work. Whether you're editing videos, working with design software, or running simulations, performance consistency is critical. Chrome Remote Desktop, on the other hand, is not designed for these scenarios. It works, but not comfortably.
If you rely heavily on Google services or use a Chromebook, Chrome Remote Desktop integrates naturally into your workflow. It's lightweight, requires no additional setup, and feels like an extension of the browser itself. In this scenario, it remains a very practical choice.
Mobile usage highlights another important difference. While remote desktop Chrome iPhone, and Chrome Remote Desktop iPad are functional, they often feel like simplified versions of the desktop experience. Controls can be less intuitive, and performance may vary depending on the connection.
DeskIn, by contrast, is designed with cross-device interaction in mind, offering a smoother and more responsive mobile experience.
👀 You may also be interested in:
Yes. Tools like DeskIn offer better performance, more features, and improved stability, especially for professional use cases.
No, Chrome Remote Desktop is still actively maintained by Google. It continues to receive security updates and remains available for users needing simple, free remote access.
Yes, DeskIn is a legitimate remote desktop solution. It uses encryption to secure connections and provides access controls, making it safe for both personal and professional use.
When comparing DeskIn vs Chrome Remote Desktop, the choice depends on how demanding your remote access needs are. Chrome Remote Desktop is simple, free, and ideal for occasional use, especially if you just need quick access to a device without extra setup.
As your workflow becomes more intensive, the limitations start to surface. DeskIn offers a smoother, more stable experience with better performance and control, making it a strong long-term Chrome remote desktop alternative for users who rely on remote access every day.


8 Best Remote Desktops for Video Editing in 2026
Remote video editing is no longer a compromise; it's a workflow upgrade. Whether you're working in Adobe Premiere Pro, After Effects, or DaVinci Resolve, the right remote desktop can turn your laptop into a high-performance editing station.
But not all tools are built for remote video editing collaboration. Lag, poor color accuracy, and unstable connections can ruin productivity. In this guide, we'll break down the best remote desktop for video editing tools so that you can edit smoothly from anywhere.
Modern creators are no longer tied to a single workstation. With remote work software, you can access your powerful desktop from anywhere without investing in an expensive laptop. For many editors, especially freelancers and small teams, this solves a real problem: you already have a high-performance PC, but mobility is limited. Instead of duplicating hardware, video editing remote desktop tools let you stream your workflow in real time.
Another key benefit is remote collaboration. Teams can work on the same project across different locations, review edits instantly, and avoid large file transfers via remote collaboration tools. However, this only works if your remote desktop software supports high frame rates, low latency, and stable connections. Otherwise, editing becomes frustrating.

Here's a quick overview of the best tools and who they're for:
DeskIn – Best overall for performance + affordability + multi-device workflows
Parsec – Best for ultra-low latency editing
Splashtop – Best for high-resolution streaming
HP Anyware – Best for enterprise-level workflows
Jump Desktop – Best for Mac users
AnyDesk – Best lightweight remote access
Chrome Remote Desktop – Best free basic option
RustDesk – Best open-source alternative
Up to 4K 60FPS / 2K 240FPS performance
Ultra-low latency for smooth editing timelines
Multi-device support (PC, Mac, iPad, Android)
Affordable pricing with free plan available
Smaller brand awareness compared to legacy tools

DeskIn stands out as the best remote desktop for video editing by balancing performance, stability, and accessibility. Unlike many traditional remote support tools, it is designed for high-frame-rate tasks, making timeline scrubbing, preview playback, and effects editing feel responsive and fluid.
For creators working across devices, DeskIn enables seamless remote video editing collaboration. You can access your main editing PC from a laptop, tablet, or even a secondary workstation without noticeable lag. Compared to tools like Chrome Remote Desktop, which struggle with video-heavy workloads, DeskIn maintains consistent quality and responsiveness—making it a practical choice for both solo editors and distributed teams.

Extremely low latency
High frame rate streaming
Popular among creative professionals
Limited collaboration features
Setup can be complex for beginners
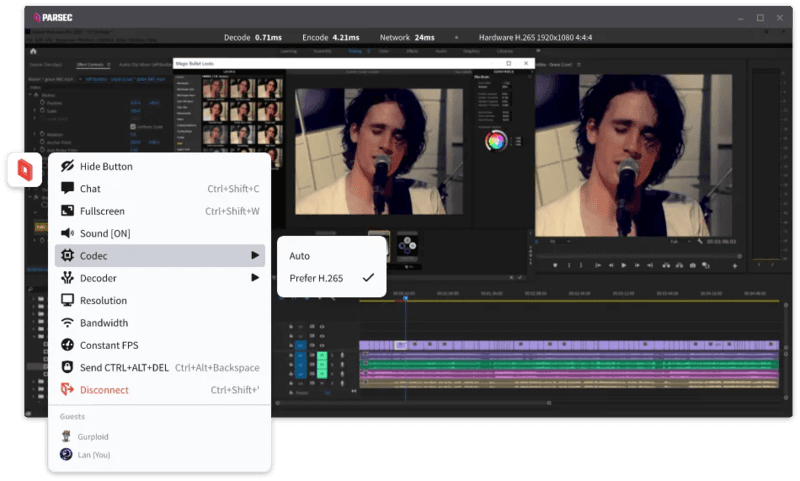
Parsec is widely recognized as a top choice for remote video editing, especially when latency is your biggest concern. Its streaming technology is optimized for real-time responsiveness, which makes it ideal for tasks like timeline scrubbing and motion graphics work in After Effects.
However, while Parsec excels in performance, it lacks some features needed for full remote video editing collaboration. Multi-user workflows and advanced access control are not as robust as some newer tools. For users who need both performance and flexibility, alternatives like DeskIn may provide a more balanced solution.
Supports 4K streaming
Strong color accuracy
Reliable for creative tasks
Higher cost for advanced features
Can experience latency over long distances

Splashtop is a solid option for editors who prioritize visual fidelity. Its support for high-resolution streaming and 4:4:4 color makes it suitable for color grading and detailed editing work.
That said, performance consistency can vary depending on network conditions. Some users report lag when working outside local networks. Compared to more optimized remote work software like DeskIn, Splashtop may require a stronger connection to maintain the same level of smoothness.
Industry-grade performance
Secure and scalable
Used in professional studios
Expensive
Complex setup
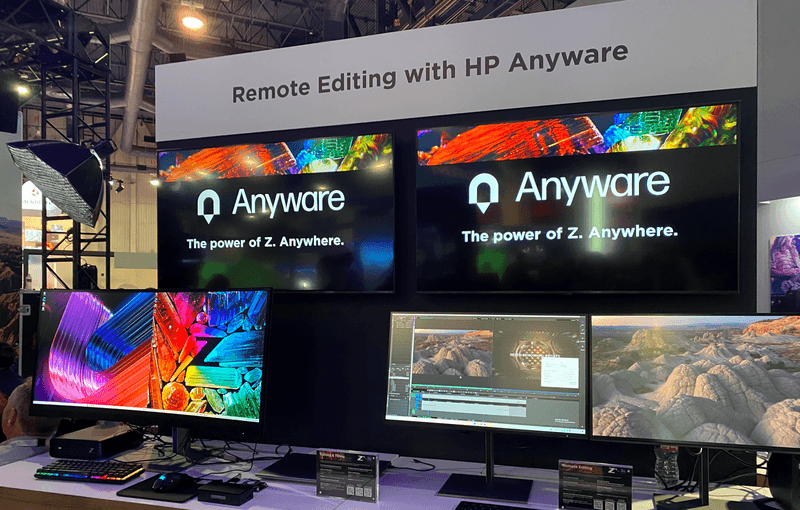
HP Anyware (formerly Teradici) is designed for high-end production environments. It uses advanced protocols to deliver excellent performance and security, making it a common choice in the media and entertainment industries.
However, for small teams or individual creators, it may be overkill. The cost and setup complexity make it less accessible compared to modern remote desktops for video editing tools that offer similar performance with easier deployment. The high cost and technical complexity create barriers that modern remote desktop solutions have eliminated, like DeskIn, offering comparable performance with far simpler deployment.
Great macOS integration
Smooth performance
Easy to use
Limited advanced features
Not ideal for heavy collaboration
Jump Desktop has earned a loyal following among Mac users seeking a straightforward, efficient remote desktop for video editing. Its Fluid Remote Desktop protocol provides smooth, responsive performance for most editing tasks without unnecessary complexity.
Where it falls short is in collaboration. Jump Desktop is built for individual use, lacking the team-oriented features that creative groups need. For solo professionals, it works well, but teams will quickly miss real-time collaboration tools found on other platforms.
Pros
Fast and lightweight
Easy to set up
Works on multiple devices
Cons
Limited performance for video editing
Lower visual quality
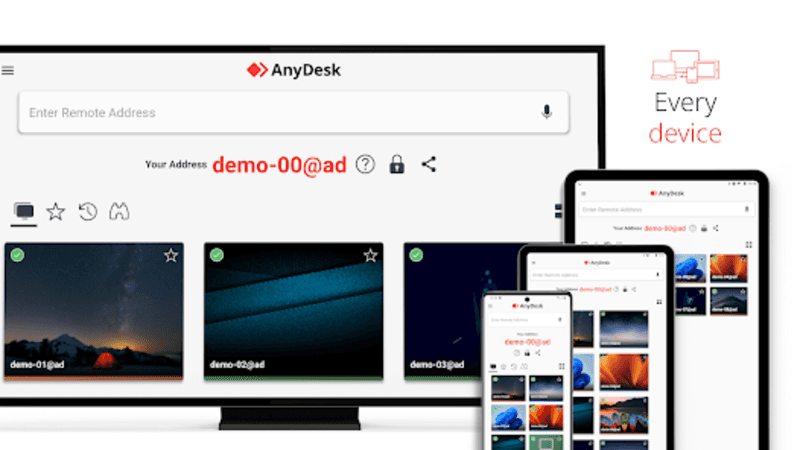
AnyDesk has built its reputation on lightweight design and remarkable ease of use for general remote access. It handles everyday tasks competently, connecting quickly and running smoothly on modest hardware.
The limitations become apparent with demanding creative work. Remote video editing requires consistent frame rates and crystal-clear visuals—areas where AnyDesk struggles. For professional editors who need precision, the performance gap becomes impossible to ignore.
Completely free
Easy browser-based setup
Works on any device
Poor performance for editing
Limited features
Chrome Remote Desktop is one of the most accessible remote support tools, offering a simple way to access your computer from anywhere. It's free, requires almost no setup, and lets you access your computer from anywhere with just a browser. For basic technical support or quick file grabs, it gets the job done.
However, it is not built for remote video editing. Users often experience lag, compression artifacts, and low frame rates. If you're working on professional projects, upgrading to a more capable solution is highly recommended.
Open-source
Self-hosting available
Free to use
Requires technical setup
Performance can vary
RustDesk appeals to users who prioritize open-source philosophy and want complete control over their remote access infrastructure. The flexibility to self-host and customize is genuinely valuable for privacy-conscious users. RustDesk is an interesting option for users who prefer open-source remote desktop not working alternatives or want full control over their infrastructure.
Performance, however, depends entirely on your configuration skills. Without technical expertise, achieving the smooth, low-latency experience required for professional editing is challenging. It's powerful for those who know how to tune it, but not plug-and-play.
Yes, with the right remote desktop for video editing, you can edit videos smoothly from anywhere. Tools like DeskIn and Parsec provide low latency and high frame rates for professional workflows.
Free options like Chrome Remote Desktop exist, but they lack performance. DeskIn offers a free plan with better performance, making it a stronger choice for real editing work.
Yes, Parsec is excellent for low-latency editing. However, it may lack collaboration features needed for team workflows.
Common issues include poor network connection, low bandwidth, or software limitations. Choosing optimized remote work software like DeskIn can significantly improve performance.
Choosing the best remote desktop for video editing depends on your workflow, budget, and performance needs. While tools like Parsec and Splashtop excel in specific areas, many solutions struggle to balance performance, stability, and usability.
If you're looking for a well-rounded solution, DeskIn offers a strong combination of high performance, smooth streaming, and cross-device flexibility. Whether you're working solo or collaborating remotely, it provides a reliable foundation for modern remote video editing workflows.

Products
Tải xuống
Resources
Contact Us
Email: support@deskin.io
Office: 991D Alexandra Road #02-17, Singapore 119972
Copyright © 2026 Zuler Technology PTE. LTD. All rights reserved.
Contact Us
Email: support@deskin.io
Office: 991D Alexandra Road #02-17, Singapore 119972
Products
Tải xuống
Resources
Copyright © 2026 Zuler Technology PTE. LTD. All rights reserved.
Products
Tải xuống
Resources
Contact Us
support@deskin.io
991D Alexandra Road #02-17
Singapore 119972
Copyright © 2026 Zuler Technology PTE. LTD. All rights reserved.