Computer na Naka-remote Control? Isang Kumpletong Gabay upang Tukuyin, Hadlangan, at Pigilan ang Remote Monitoring
W. Ting
/
10 minuto
/
Na-update
Sa mga nakaraang taon, ang mga paglabag sa data ay naging labis na nakakabahala. Sa nakaraang taon lamang, higit sa 1 bilyong tala ang nakuha ng mga hacker — isang talagang nakakagulat na bilang. Ang mas nakababahala pa ay ang mga remote control attack sa mga computer ay mas madalas na ngayon kaysa dati.
Ayon sa isang pag-aaral ng Check Point Research, sa pagitan ng Agosto 2024 at Enero 2025, ang tatlong pangunahing target para sa mga cyberattack sa Taiwan ay mga tagapagtustos ng hardware, mga ahensya ng gobyerno at militar, at ang industriya ng pagmamanupaktura. Kung ikaw ay isang indibidwal o isang negosyo, panahon na upang seryosohin ang seguridad ng computer.
Kung ang iyong computer ay kumikilos ng kakaiba — halimbawa, ang iyong mouse ay kumikilos nang kusa, ang mga file ay mahiwagang nabago, o ang sistema ay biglang bumabagal — maaaring ito ay isang senyales ng pagpasok ng hacker. Kung minsan, ang isang remote desktop program na ginamit mo noon ay maaaring patuloy na tumatakbo nang lihim sa background. Kapag ang iyong sistema ay nasa ilalim ng mapanlinlang na remote control, hindi lamang maaaring makuha ang iyong personal na data, kundi ang iyong computer ay maaari ring magamit bilang kasangkapan upang atakihin ang iba.
Ang artikulong ito ay nagbibigay ng kumpletong gabay kung paano matukoy, harangan, at pigilan ang mga ganitong banta — tinutulungan kang makuha muli ang kontrol ng iyong computer.
Kaugnay na Pagbasa:
Paano Matukoy Kung Ang Iyong Computer Ay Nasa Remote Control
Kung pinaghihinalaan mong ang iyong computer ay ina-access nang remote, ang unang hakbang ay matutunan kung paano ito matutukoy. Sa kabutihang-palad, maaari mong gamitin ang mga built-in na tool at utos ng sistema upang mabilis na suriin kung may lihim na uma-access sa iyong aparato.
Matukoy ang Remote Control sa Windows
Ang Windows ay nagbibigay ng ilang mga built-in na tool para sa inspeksyon ng sistema. Ang sumusunod na tatlong pamamaraan ay makakatulong sa iyo na mabilis na makilala ang mga hindi karaniwang remote na koneksyon.
Paraan 1: Suriin ang Mga Nakalog-in na Gumagamit sa pamamagitan ng Command Prompt
Pindutin ang Win + R upang buksan ang Run dialog box, i-type ang cmd, at pindutin ang Enter.
Sa Command Prompt window, ipasok ang mga sumusunod na utos:
Code block
1 quser
2 query user
Surin ang mga resulta — kung makakita ka ng hindi pamilyar na mga account na kasalukuyang nakalog-in, maaaring ito ay nagpapahiwatig na ang iyong computer ay ina-access nang remote.
Paraan 2: Suriin ang Mga Aktibong Gumagamit sa pamamagitan ng Task Manager
Ito ay isang tuwirang at real-time na paraan upang makita ang lahat ng nakalog-in na gumagamit.
Pindutin ang Ctrl + Shift + Esc upang buksan ang Task Manager.
Pumunta sa tab na Users.
Surin ang listahan — sa normal na mga kalagayan, dapat mong makita lamang ang iyong kasalukuyang account.
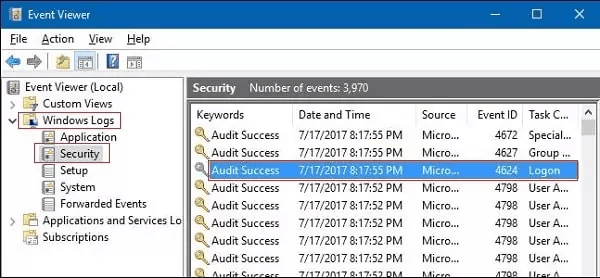
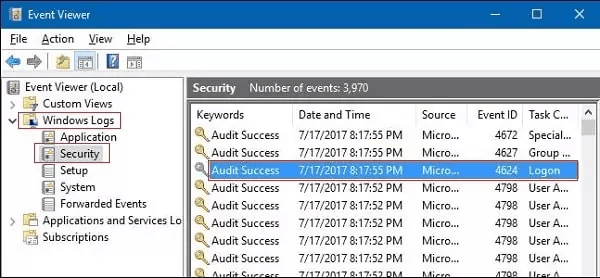
Paraan 3: Subaybayan ang Kasaysayan ng Pag-log sa pamamagitan ng Event Viewer
Ang Event Viewer ay nagbibigay ng detalyadong mga log ng aktibidad ng sistema, na ginagawang perpekto para sa pagsubaybay sa pag-uugali ng pag-log.
Hanapin at buksan ang Event Viewer mula sa Start menu.
Pumunta sa Windows Logs > Security.
Tingnan ang Event ID 4624 (Matagumpay na Pag-log) at suriin ang mga kahina-hinalang remote na entry ng pag-login.
Matukoy ang Remote Control sa macOS
Habang ang macOS ay gumagamit ng ibang diskarte, ang batayang lohika ay pareho — pagtukoy sa mga senyales ng hindi awtorisadong pag-access.
Paraan 1: Suriin ang Mga Setting ng Screen Sharing
Pumunta sa System Preferences > Sharing.
Kumpirmahin na ang Screen Sharing at Remote Login ay naka-off.
Kung ang mga serbisyong ito ay pinagana nang walang iyong kaalaman, maaaring compromised ang iyong sistema — patayin ang mga ito agad.
Paraan 2: I-monitor ang Mga Koneksyon sa Network
Gamitin ang built-in na Activity Monitor upang obserbahan ang paggamit ng network at tukuyin ang anumang kakaibang aktibidad.
Paano Harangan ang Remote Control sa Iyong Computer
Kapag napatunayan mo na ang iyong computer ay nasa remote control, panahon na para sa agarang aksyon. Kung gumagamit ka ng Windows o Mac, ang mga pamamaraang ito ay makakatulong sa iyong putulin ang koneksyon at ihinto ang karagdagang kontrol.
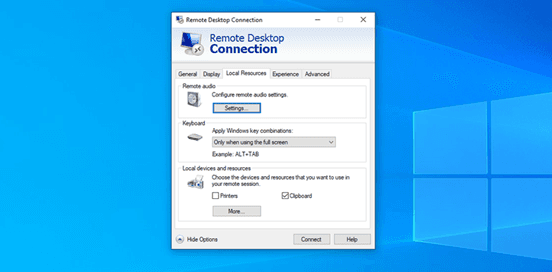
Itigil ang Remote Access sa Windows
Madaling sinasamantala ng mga hacker ang built-in na Remote Desktop at Remote Assistance na mga tampok ng Windows. Ang pag-disable ng mga ito ay ang unang hakbang patungo sa mas malakas na proteksyon.
Paraan 1: I-disable ang Remote Desktop at Remote Assistance
Ito ang pinakamadaling paraan upang harangan ang hindi awtorisadong pag-access.
Pindutin ang Win + R, i-type ang control, at pindutin ang Enter.
Pumunta sa System and Security > System > Remote settings.
Sa Remote tab, i-uncheck ang Payagan ang mga koneksyon ng Remote Assistance sa computer na ito.
Pumili ng Huwag payagan ang mga remote na koneksyon sa computer na ito at i-click ang OK.
Paraan 2: Ayusin ang Mga Setting ng Windows Firewall
Kahit na na-disable mo ang mga remote na tampok, maaari kang magdagdag ng karagdagang proteksyon sa pamamagitan ng firewall.
Buksan ang Windows Defender Firewall.
I-click ang Payagan ang isang app o tampok sa pamamagitan ng Windows Defender Firewall.
I-click ang Baguhin ang mga setting, pagkatapos ay i-uncheck ang Remote Assistance at Remote Desktop.
I-save ang iyong mga pagbabago.
Paraan 3: I-disable ang mga Hindi Kinakailangang Remote Services
Gamitin ang Services Manager upang ganap na i-disable ang mga remote-related na background services.
Pindutin ang Win + R, i-type ang services.msc, at pindutin ang Enter.
Hanapin at i-disable ang mga sumusunod na serbisyo:
Remote Desktop Services
Remote Registry
Telnet (kung naka-enable)
I-set ang kanilang startup type sa Disabled.
Itigil ang Remote Access sa Mac
Ang macOS ay namamahala ng remote access nang sentral sa pamamagitan ng System Preferences.
Paraan 1: I-disable ang mga Tampok ng Remote Access
Pumunta sa System Preferences > Sharing.
I-uncheck ang mga sumusunod:
Screen Sharing
Remote Login
Remote Management
Remote Apple Events
Tiyakin na ang lahat ng pagpipilian sa remote access ay naka-off.
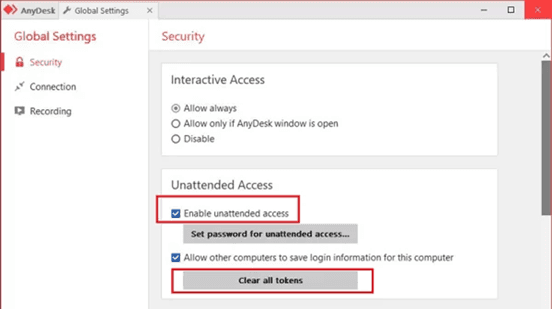
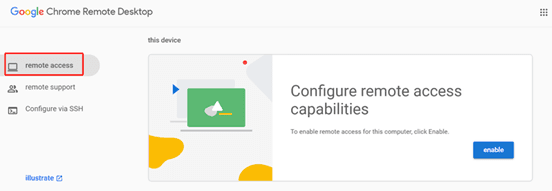
Paraan 2: Suriin at Alisin ang Hindi Kilalang Apps
Maaaring may mga remote control apps na na-install nang walang iyong pahintulot.
Pumunta sa Applications folder.
Hanapin ang mga hindi pamilyar na software ng remote control — tulad ng TeamViewer, AnyDesk, o Chrome Remote Desktop.
Kung hindi mo sila na-install, alisin ang mga ito agad.
Paano Pigilan ang Mga Hinaharap na Pag-atake ng Remote Control
Hindi sapat ang mga agarang aksyon lamang — ang pangmatagalang proteksyon ay susi. Ang pagbuo ng isang multi-layered security strategy ay makakapagpababa ng iyong panganib sa mga pag-atake ng remote access.
Palakasin ang Authentication
Gumamit ng kumplikadong at natatanging mga password na may uppercase, lowercase, mga numero, at mga simbolo.
I-enable ang two-factor authentication (2FA).
Palitan ang mga password nang regular at iwasan ang paggamit ng parehong password sa maraming serbisyo.
Pamahalaan ang Mga Update at Patches
Noong 2024, sinamantala ng mga hacker ang 768 na kahinaan na may mga numero ng CVE — isang 20% na pagtaas mula 2023. Mahalagang panatilihing updated ang iyong sistema.
I-enable ang automated na mga update ng sistema.
Regular na i-install ang mga security patches.
Panatilihing updated ang iyong mga antivirus definitions.
Palakasin ang Seguridad ng Network
Gumamit ng VPN upang i-encrypt ang iyong koneksyon, lalo na sa pampublikong Wi-Fi.
Iwasan ang mga hindi ligtas na pampublikong network.
Palitan ang default na password ng iyong router at i-review ang mga setting nang regular.
Mag-install ng mapagkakatiwalaang antivirus software na may real-time na proteksyon.
Magpatakbo ng buong system scans nang regular.
Gumamit ng secure remote desktop software na may encrypted connections.
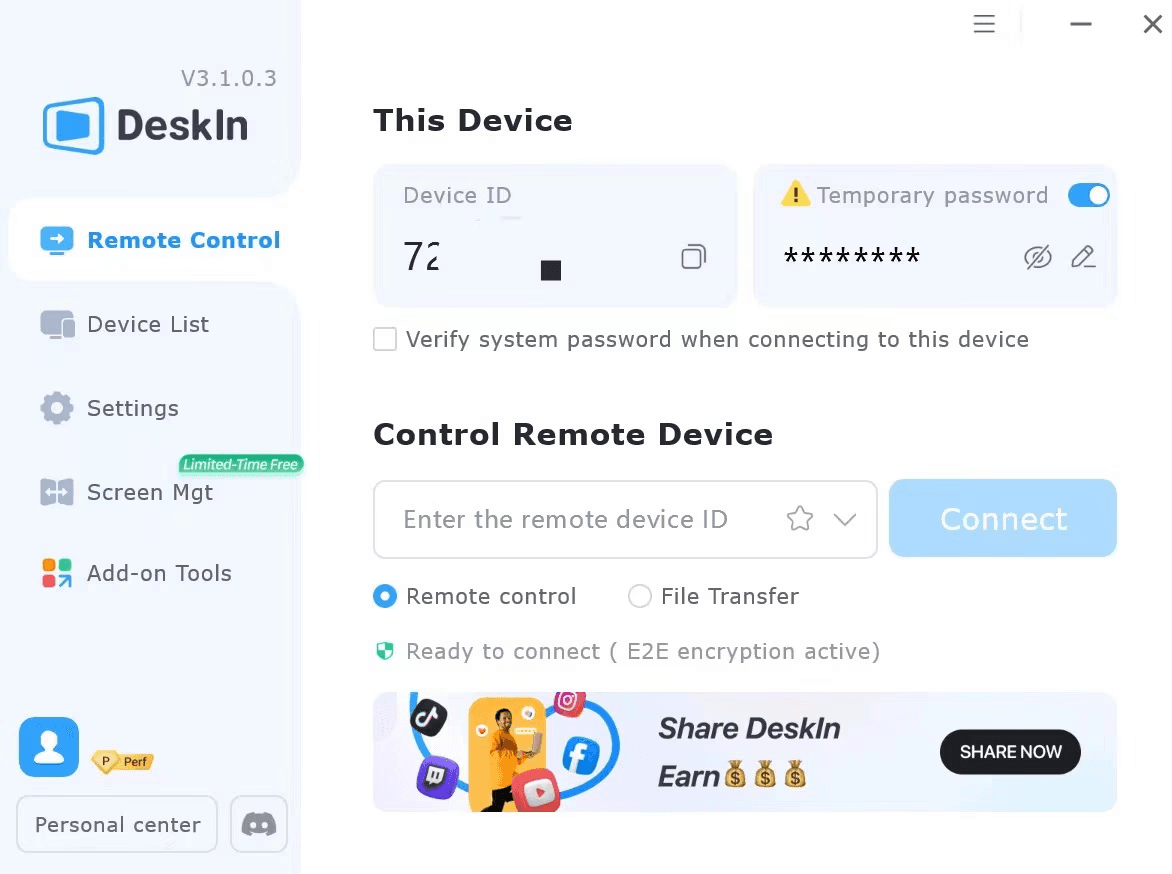
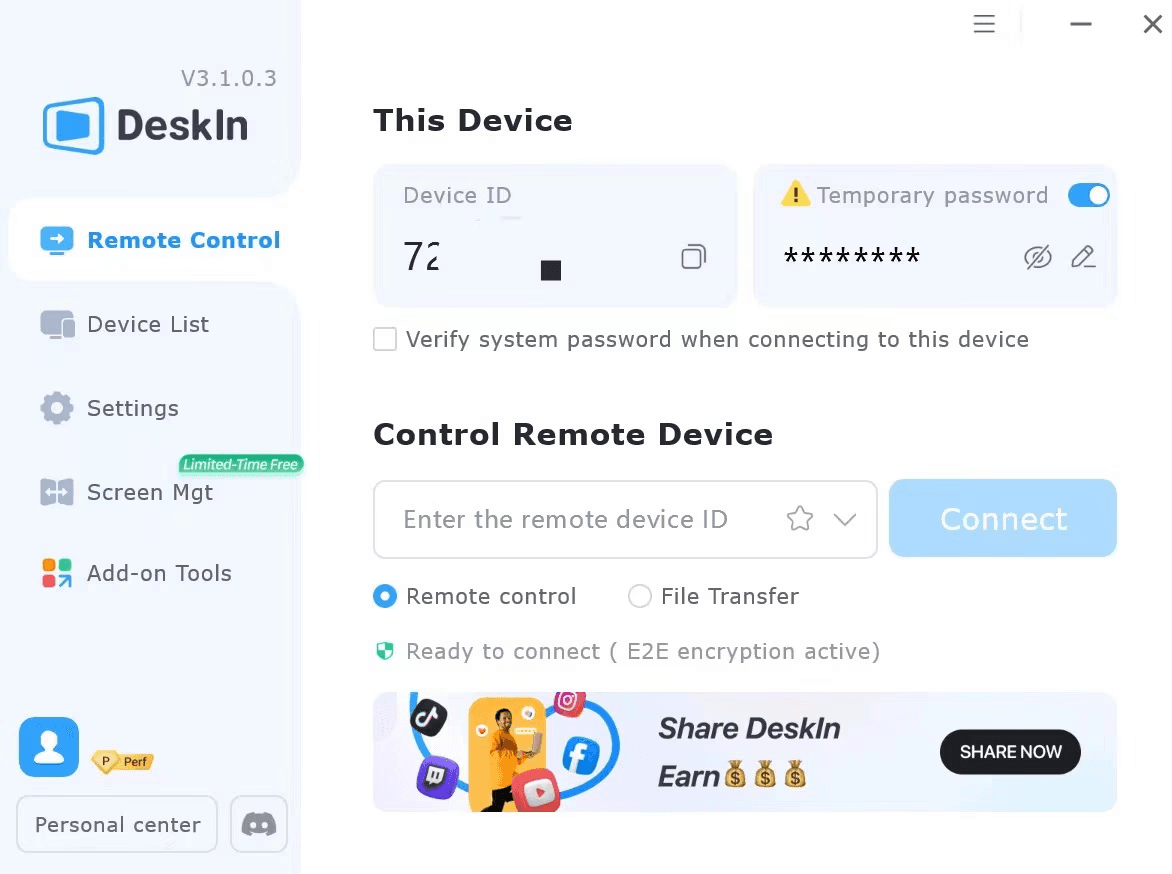
Gumamit ng DeskIn para sa Secure Remote Access
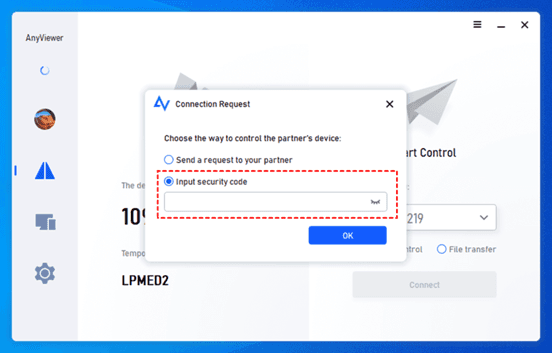
Kung talagang kailangan mong ma-access ang iyong computer nang remote, pumili ng maingat sa iyong software. Maraming remote na tool ang nagdadala ng mga panganib sa seguridad — kaya't gamitin lamang ang mga may malalakas na tampok sa proteksyon.
Sa maraming mga opsyon, ang DeskIn ay namumukod-tangi para sa matibay na pundasyon ng seguridad nito. Gumagamit ito ng advanced AES-256 end-to-end encryption upang protektahan ang paglipat ng data, kasama ang two-factor authentication upang matiyak na ang mga awtorisadong gumagamit lamang ang maaaring kumonekta. Kung ikukumpara sa mga tool na kilala para sa mga kahinaan sa seguridad, nag-aalok ang DeskIn ng kapanatagan.
Mga Key Security Features ng DeskIn:
End-to-end AES-256 Encryption: Tinitiyak ang ligtas na paglipat ng data, pinipigilan ang pakikinig o man-in-the-middle na mga pag-atake.
Multi-factor Authentication: Suportado ang mga pansamantalang password, mga security code, o 2FA para sa nababaluktot na mga antas ng seguridad.
Whitelist/Blacklist na Access Control: Pamahalaan kung aling mga gumagamit o aparato ang maaaring kumonekta.
Privacy Screen at Auto-Lock: Awtomatikong nag-aaktibo ng privacy screen sa panahon ng mga remote session at nilalak ang screen pagkatapos.
Proteksyon ng Account: Awtomatikong nilalak ang DeskIn kapag may mga hindi awtorisadong account na sumusubok kumonekta.
Paano Ligtas na Gamitin ang DeskIn para sa Remote Access
I-download ang DeskIn lamang mula sa opisyal na website.
Magparehistro at mag-set ng malakas na password, pagkatapos ay i-enable ang 2FA.
I-configure ang mga pahintulot ng access at mga setting ng seguridad batay sa iyong mga pangangailangan.
Gumamit ng siguradong connection code o pamamaraan ng account binding para sa remote access.
Konklusyon
Pagdating sa cybersecurity, ang mga gawi ang pinakamahalaga. Walang permanenteng solusyon — nangangailangan ito ng patuloy na atensyon at regular na mga update. Ang pagiging mapagbantay at regular na pagsusuri sa iyong sistema ay makakatulong sa iyo na mag-enjoy ng digital convenience nang hindi nag-aalala tungkol sa mga paglabag sa data o pag-hack.
Kung kailangan mo ng remote access para sa trabaho, ang pagpili ng tamang tool ay mahalaga. Ang software tulad ng DeskIn, na may komprehensibong mekanismo ng seguridad, ay nagpapahintulot sa iyo na magtrabaho nang mahusay habang pinapaliit ang panganib ng pagiging remotely controlled.
Sa tamang pag-iisip at mapagkakatiwalaang mga tool, ang remote technology ay maaari mong maging Ally — hindi isang banta sa seguridad.
📥 Nais bang subukan ito? Nag-aalok ang DeskIn ng libreng bersyon — enterprise-grade na encryption, ligtas at secure na gamitin!
Sa mga nakaraang taon, ang mga paglabag sa data ay naging labis na nakakabahala. Sa nakaraang taon lamang, higit sa 1 bilyong tala ang nakuha ng mga hacker — isang talagang nakakagulat na bilang. Ang mas nakababahala pa ay ang mga remote control attack sa mga computer ay mas madalas na ngayon kaysa dati.
Ayon sa isang pag-aaral ng Check Point Research, sa pagitan ng Agosto 2024 at Enero 2025, ang tatlong pangunahing target para sa mga cyberattack sa Taiwan ay mga tagapagtustos ng hardware, mga ahensya ng gobyerno at militar, at ang industriya ng pagmamanupaktura. Kung ikaw ay isang indibidwal o isang negosyo, panahon na upang seryosohin ang seguridad ng computer.
Kung ang iyong computer ay kumikilos ng kakaiba — halimbawa, ang iyong mouse ay kumikilos nang kusa, ang mga file ay mahiwagang nabago, o ang sistema ay biglang bumabagal — maaaring ito ay isang senyales ng pagpasok ng hacker. Kung minsan, ang isang remote desktop program na ginamit mo noon ay maaaring patuloy na tumatakbo nang lihim sa background. Kapag ang iyong sistema ay nasa ilalim ng mapanlinlang na remote control, hindi lamang maaaring makuha ang iyong personal na data, kundi ang iyong computer ay maaari ring magamit bilang kasangkapan upang atakihin ang iba.
Ang artikulong ito ay nagbibigay ng kumpletong gabay kung paano matukoy, harangan, at pigilan ang mga ganitong banta — tinutulungan kang makuha muli ang kontrol ng iyong computer.
Kaugnay na Pagbasa:
Paano Matukoy Kung Ang Iyong Computer Ay Nasa Remote Control
Kung pinaghihinalaan mong ang iyong computer ay ina-access nang remote, ang unang hakbang ay matutunan kung paano ito matutukoy. Sa kabutihang-palad, maaari mong gamitin ang mga built-in na tool at utos ng sistema upang mabilis na suriin kung may lihim na uma-access sa iyong aparato.
Matukoy ang Remote Control sa Windows
Ang Windows ay nagbibigay ng ilang mga built-in na tool para sa inspeksyon ng sistema. Ang sumusunod na tatlong pamamaraan ay makakatulong sa iyo na mabilis na makilala ang mga hindi karaniwang remote na koneksyon.
Paraan 1: Suriin ang Mga Nakalog-in na Gumagamit sa pamamagitan ng Command Prompt
Pindutin ang Win + R upang buksan ang Run dialog box, i-type ang cmd, at pindutin ang Enter.
Sa Command Prompt window, ipasok ang mga sumusunod na utos:
Code block
1 quser
2 query user
Surin ang mga resulta — kung makakita ka ng hindi pamilyar na mga account na kasalukuyang nakalog-in, maaaring ito ay nagpapahiwatig na ang iyong computer ay ina-access nang remote.
Paraan 2: Suriin ang Mga Aktibong Gumagamit sa pamamagitan ng Task Manager
Ito ay isang tuwirang at real-time na paraan upang makita ang lahat ng nakalog-in na gumagamit.
Pindutin ang Ctrl + Shift + Esc upang buksan ang Task Manager.
Pumunta sa tab na Users.
Surin ang listahan — sa normal na mga kalagayan, dapat mong makita lamang ang iyong kasalukuyang account.
Paraan 3: Subaybayan ang Kasaysayan ng Pag-log sa pamamagitan ng Event Viewer
Ang Event Viewer ay nagbibigay ng detalyadong mga log ng aktibidad ng sistema, na ginagawang perpekto para sa pagsubaybay sa pag-uugali ng pag-log.
Hanapin at buksan ang Event Viewer mula sa Start menu.
Pumunta sa Windows Logs > Security.
Tingnan ang Event ID 4624 (Matagumpay na Pag-log) at suriin ang mga kahina-hinalang remote na entry ng pag-login.
Matukoy ang Remote Control sa macOS
Habang ang macOS ay gumagamit ng ibang diskarte, ang batayang lohika ay pareho — pagtukoy sa mga senyales ng hindi awtorisadong pag-access.
Paraan 1: Suriin ang Mga Setting ng Screen Sharing
Pumunta sa System Preferences > Sharing.
Kumpirmahin na ang Screen Sharing at Remote Login ay naka-off.
Kung ang mga serbisyong ito ay pinagana nang walang iyong kaalaman, maaaring compromised ang iyong sistema — patayin ang mga ito agad.
Paraan 2: I-monitor ang Mga Koneksyon sa Network
Gamitin ang built-in na Activity Monitor upang obserbahan ang paggamit ng network at tukuyin ang anumang kakaibang aktibidad.
Paano Harangan ang Remote Control sa Iyong Computer
Kapag napatunayan mo na ang iyong computer ay nasa remote control, panahon na para sa agarang aksyon. Kung gumagamit ka ng Windows o Mac, ang mga pamamaraang ito ay makakatulong sa iyong putulin ang koneksyon at ihinto ang karagdagang kontrol.
Itigil ang Remote Access sa Windows
Madaling sinasamantala ng mga hacker ang built-in na Remote Desktop at Remote Assistance na mga tampok ng Windows. Ang pag-disable ng mga ito ay ang unang hakbang patungo sa mas malakas na proteksyon.
Paraan 1: I-disable ang Remote Desktop at Remote Assistance
Ito ang pinakamadaling paraan upang harangan ang hindi awtorisadong pag-access.
Pindutin ang Win + R, i-type ang control, at pindutin ang Enter.
Pumunta sa System and Security > System > Remote settings.
Sa Remote tab, i-uncheck ang Payagan ang mga koneksyon ng Remote Assistance sa computer na ito.
Pumili ng Huwag payagan ang mga remote na koneksyon sa computer na ito at i-click ang OK.
Paraan 2: Ayusin ang Mga Setting ng Windows Firewall
Kahit na na-disable mo ang mga remote na tampok, maaari kang magdagdag ng karagdagang proteksyon sa pamamagitan ng firewall.
Buksan ang Windows Defender Firewall.
I-click ang Payagan ang isang app o tampok sa pamamagitan ng Windows Defender Firewall.
I-click ang Baguhin ang mga setting, pagkatapos ay i-uncheck ang Remote Assistance at Remote Desktop.
I-save ang iyong mga pagbabago.
Paraan 3: I-disable ang mga Hindi Kinakailangang Remote Services
Gamitin ang Services Manager upang ganap na i-disable ang mga remote-related na background services.
Pindutin ang Win + R, i-type ang services.msc, at pindutin ang Enter.
Hanapin at i-disable ang mga sumusunod na serbisyo:
Remote Desktop Services
Remote Registry
Telnet (kung naka-enable)
I-set ang kanilang startup type sa Disabled.
Itigil ang Remote Access sa Mac
Ang macOS ay namamahala ng remote access nang sentral sa pamamagitan ng System Preferences.
Paraan 1: I-disable ang mga Tampok ng Remote Access
Pumunta sa System Preferences > Sharing.
I-uncheck ang mga sumusunod:
Screen Sharing
Remote Login
Remote Management
Remote Apple Events
Tiyakin na ang lahat ng pagpipilian sa remote access ay naka-off.
Paraan 2: Suriin at Alisin ang Hindi Kilalang Apps
Maaaring may mga remote control apps na na-install nang walang iyong pahintulot.
Pumunta sa Applications folder.
Hanapin ang mga hindi pamilyar na software ng remote control — tulad ng TeamViewer, AnyDesk, o Chrome Remote Desktop.
Kung hindi mo sila na-install, alisin ang mga ito agad.
Paano Pigilan ang Mga Hinaharap na Pag-atake ng Remote Control
Hindi sapat ang mga agarang aksyon lamang — ang pangmatagalang proteksyon ay susi. Ang pagbuo ng isang multi-layered security strategy ay makakapagpababa ng iyong panganib sa mga pag-atake ng remote access.
Palakasin ang Authentication
Gumamit ng kumplikadong at natatanging mga password na may uppercase, lowercase, mga numero, at mga simbolo.
I-enable ang two-factor authentication (2FA).
Palitan ang mga password nang regular at iwasan ang paggamit ng parehong password sa maraming serbisyo.
Pamahalaan ang Mga Update at Patches
Noong 2024, sinamantala ng mga hacker ang 768 na kahinaan na may mga numero ng CVE — isang 20% na pagtaas mula 2023. Mahalagang panatilihing updated ang iyong sistema.
I-enable ang automated na mga update ng sistema.
Regular na i-install ang mga security patches.
Panatilihing updated ang iyong mga antivirus definitions.
Palakasin ang Seguridad ng Network
Gumamit ng VPN upang i-encrypt ang iyong koneksyon, lalo na sa pampublikong Wi-Fi.
Iwasan ang mga hindi ligtas na pampublikong network.
Palitan ang default na password ng iyong router at i-review ang mga setting nang regular.
Mag-install ng mapagkakatiwalaang antivirus software na may real-time na proteksyon.
Magpatakbo ng buong system scans nang regular.
Gumamit ng secure remote desktop software na may encrypted connections.
Gumamit ng DeskIn para sa Secure Remote Access
Kung talagang kailangan mong ma-access ang iyong computer nang remote, pumili ng maingat sa iyong software. Maraming remote na tool ang nagdadala ng mga panganib sa seguridad — kaya't gamitin lamang ang mga may malalakas na tampok sa proteksyon.
Sa maraming mga opsyon, ang DeskIn ay namumukod-tangi para sa matibay na pundasyon ng seguridad nito. Gumagamit ito ng advanced AES-256 end-to-end encryption upang protektahan ang paglipat ng data, kasama ang two-factor authentication upang matiyak na ang mga awtorisadong gumagamit lamang ang maaaring kumonekta. Kung ikukumpara sa mga tool na kilala para sa mga kahinaan sa seguridad, nag-aalok ang DeskIn ng kapanatagan.
Mga Key Security Features ng DeskIn:
End-to-end AES-256 Encryption: Tinitiyak ang ligtas na paglipat ng data, pinipigilan ang pakikinig o man-in-the-middle na mga pag-atake.
Multi-factor Authentication: Suportado ang mga pansamantalang password, mga security code, o 2FA para sa nababaluktot na mga antas ng seguridad.
Whitelist/Blacklist na Access Control: Pamahalaan kung aling mga gumagamit o aparato ang maaaring kumonekta.
Privacy Screen at Auto-Lock: Awtomatikong nag-aaktibo ng privacy screen sa panahon ng mga remote session at nilalak ang screen pagkatapos.
Proteksyon ng Account: Awtomatikong nilalak ang DeskIn kapag may mga hindi awtorisadong account na sumusubok kumonekta.
Paano Ligtas na Gamitin ang DeskIn para sa Remote Access
I-download ang DeskIn lamang mula sa opisyal na website.
Magparehistro at mag-set ng malakas na password, pagkatapos ay i-enable ang 2FA.
I-configure ang mga pahintulot ng access at mga setting ng seguridad batay sa iyong mga pangangailangan.
Gumamit ng siguradong connection code o pamamaraan ng account binding para sa remote access.
Konklusyon
Pagdating sa cybersecurity, ang mga gawi ang pinakamahalaga. Walang permanenteng solusyon — nangangailangan ito ng patuloy na atensyon at regular na mga update. Ang pagiging mapagbantay at regular na pagsusuri sa iyong sistema ay makakatulong sa iyo na mag-enjoy ng digital convenience nang hindi nag-aalala tungkol sa mga paglabag sa data o pag-hack.
Kung kailangan mo ng remote access para sa trabaho, ang pagpili ng tamang tool ay mahalaga. Ang software tulad ng DeskIn, na may komprehensibong mekanismo ng seguridad, ay nagpapahintulot sa iyo na magtrabaho nang mahusay habang pinapaliit ang panganib ng pagiging remotely controlled.
Sa tamang pag-iisip at mapagkakatiwalaang mga tool, ang remote technology ay maaari mong maging Ally — hindi isang banta sa seguridad.
📥 Nais bang subukan ito? Nag-aalok ang DeskIn ng libreng bersyon — enterprise-grade na encryption, ligtas at secure na gamitin!